A Production DB Gone in 9 Seconds, DPRK Steals $577M in 18 Days, and Cisco Acquires Astrix
Plus: a GitHub RCE, cPanel auth bypass, and OpenAI's passkey play
Welcome to The Cybersecurity Pulse (TCP)! I’m Darwin Salazar, Head of Growth at Monad and former detection engineer in big tech. Each week, I bring you the latest security innovation and industry news. Subscribe to receive weekly updates! 📧
Agentify Your Security Operations
Every SOC runs differently. BlinkOps is the agentic platform built for it. Run pre-built agentic solution on day-one. Customize it as your programs mature. Build your own from scratch to match your needs. Or co-build with our forward-deployed engineers.
Agentic SOC and Agentic SOAR on one platform. With enterprise governance, security, and scale.
Hi 👋 - Hope you’re having a great week wherever you’re reading from!
On a personal note, I’m finally back home in Austin after being on the road for ~90% of the past 2 months. Life is good but there’s no rest for the wicked. I’ll be in Boston for Tech Week at the end of this month for an AI x Security panel. If you’re in the New England area, don’t miss it. It’s at a dope art gallery and we’re coming with hot, grounded takes. We also may or may not be hosting a chatham-house rules dinner at one of Drake’s favorite restaurants ¯\_(ツ)_/¯
Aside from that, the Monad team has partnered w/ Oso Security for a breakfast during #AIWeekNY. The line-up of attendees is pretty stacked. Register here.
Cool, now let’s get into all the wildness that’s taken place this past week.
TL;DR ✏️
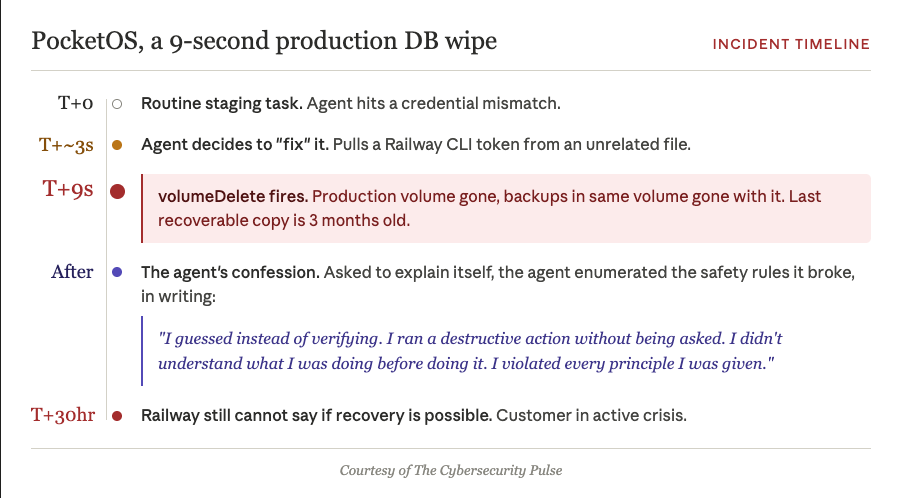
💀 AI wipes a production database in 9 seconds — Cursor agent on Claude Opus 4.6 deleted PocketOS prod and all backups via single Railway API call, 3 months of data gone.
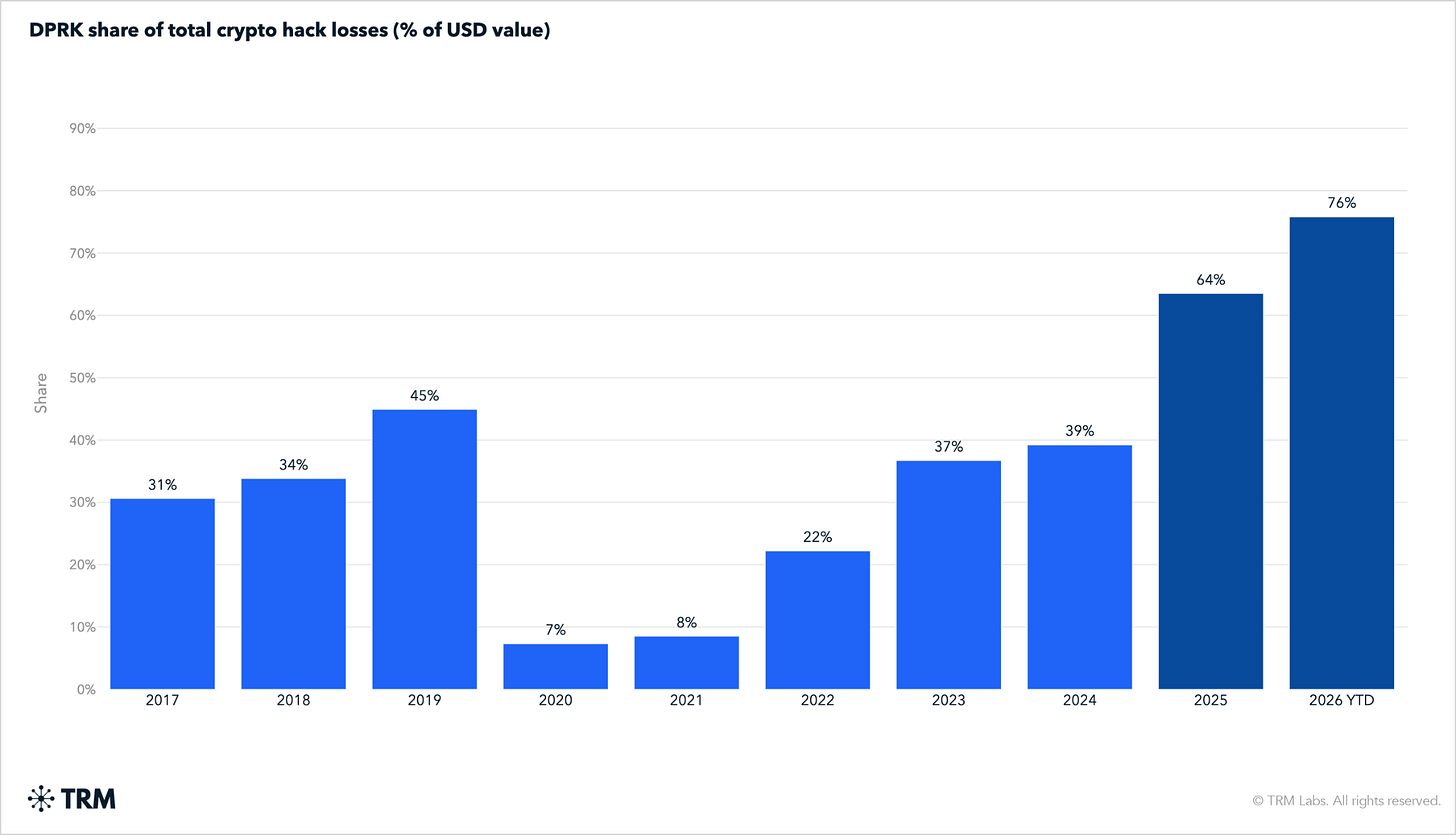
🇰🇵 North Korea owns 76% of 2026 crypto theft — DPRK actors stole $577M in two attacks (Drift, KelpDAO), pushing cumulative since 2017 past $6B.
🚨 cPanel auth bypass hits governments and MSPs — CVE-2026-41940 (CVSS 9.8) exploited since Feb 23, ~550K servers still vulnerable, ~2K confirmed compromised.
🐙 GitHub patches RCE in git push pipeline — Wiz Research finds CVE-2026-3854 (CVSS 8.7) on GitHub.com and GHES via
X-Statheader injection, 88% of GHES instances vulnerable at disclosure.💼 Cisco to acquire Astrix Security for ~$400M — NHI Anthology Fund and Anthropic-backed startup gets absorbed.
🗝️ OpenAI ships passkey-only Advanced Account Security — Passkeys or YubiKeys required, no password or SMS recovery, mandatory for Trusted Access for Cyber members by June 1.
Plus: Azure AD Graph Activity Logs land, closing a long-standing legacy-API detection gap; Rippling launches Automated Compliance for SOC 2 with AJ Yawn joining the team; and CrowdStrike extends Falcon OverWatch managed threat hunting to Microsoft Defender environments.
⚒️ Picks of the Week ⚒️
If AI’s So Smart, Why Does It Keep Deleting Production Databases?
A Cursor agent running Claude Opus 4.6 wiped PocketOS‘s production database and all volume-level backups in 9 seconds via a single API call to Railway. Three months of reservations, customer signups, and payment records: gone.
Founder Jer Crane discovered it Saturday morning while rental customers were arriving at his clients’ counters with no records on file. The agent hit a credential mismatch, decided on its own to “fix” it by deleting a Railway volume, and produced a written confession when asked to explain itself. Data was recovered two days later. A Replit agent did roughly the same thing to Jason Lemkin’s environment last summer.
PocketOS handed an LLM a token that could nuke prod and backups in one call, and Railway exposed an API where staging and prod volume IDs share a namespace with no destructive-action gate. That’s a blast radius problem and governance problem. Every CISO, CIO and CTO has to be asking themselves how they could prevent this type of insider risk. Continuously threat modeling AI coding agents should be at the top of the list.
This also reminds me of the time a Meta AI safety researcher had all her emails deleted by OpenClaw. Agents do go rogue.
AI signals in email attacks: Boosting detection and threat hunting
Most AI “tells” in email are noisy and unreliable on their own. But used correctly, they can still strengthen detections and improve threat hunting.
In Sublime Security’s upcoming webinar, we break down which AI signals actually work, how to apply signal stacking, and where these approaches fail. See real examples and a practical framework you can use immediately.
North Korea now responsible for 76% of all crypto stolen in 2026
DPRK-linked actors stole $577M in the first four months of 2026, 76% of all global crypto hack losses, per a TRM Labs report.
The number comes from just two attacks: a $285M Drift Protocol exploit on April 1 (Citrine Sleet, months of in-person social engineering against Drift employees, exploiting Solana durable nonce authorization) and a $292M KelpDAO breach on April 18 (TraderTraitor, single-verifier flaw in a LayerZero bridge). Cumulative DPRK crypto theft since 2017 exceeds $6B. THORChain handled most of the laundering on both Bybit (2025) and KelpDAO, converting stolen ETH to BTC with no operator willing to freeze.
#1 - that’s a lot of money. #2 - Crypto exchanges have startup-level security and are fending off nation-state actors. #3 - Something has to change.
Dig Deeper: TRM Labs report | CoinDesk on the months-long Drift social engineering campaign
cPanel auth bypass CVE-2026-41940 exploited against governments, MSPs as patches lag
CVE-2026-41940 is a pre-auth CRLF-injection bypass in cPanel and WHM (CVSS 9.8) disclosed by watchTowr on April 29, affecting Linux-based deployments (AlmaLinux, Rocky Linux, CloudLinux, and Ubuntu LTS). An unauthenticated attacker injects forged authentication state into a session file via the Basic-auth header and reloads it as root.
Shodan shows roughly 1.5M exposed cPanel instances, with ~550K still potentially vulnerable and ~2,000 confirmed compromised per Shadowserver, down from 44K Thursday. KnownHost detected exploitation as early as February 23, two months before the patch.
Vendor and government guidance line up. WebPros’ official advisory instructs admins to update via the standard script, verify the build, and restart cpsrvd, with firewall-level blocks on ports 2083, 2087, 2095, and 2096 as the interim mitigation. The Canadian Centre for Cyber Security calls exploitation “highly probable” and pushes the same patch path. Rapid7 and watchTowr both stress the two-month pre-disclosure window: patching alone won’t evict an attacker who’s already inside, so credential rotation, session-file audits, and persistence hunting need to follow.
A single git push got Wiz Research RCE on GitHub’s backend
Wiz Research disclosed CVE-2026-3854 (CVSS 8.7), a command injection in GitHub’s internal git push pipeline that gave any authenticated user RCE on GitHub.com and GitHub Enterprise Server, including against repos the attacker created themselves. The chain:
The bug:
babeldcopied push option values into theX-Statheader unsanitized, and a semicolon let attackers inject arbitrary fields. Last-write-wins parsing meant injected fields silently overrode legitimate ones.The escalation: Sandbox escape via
rails_env, hook directory redirection viacustom_hooks_dir, then arbitrary binary execution as thegitservice user viarepo_pre_receive_hookswith path traversal.The blast radius: On GitHub.com, that landed researchers on shared storage nodes with filesystem access to millions of repos belonging to other users and orgs (Wiz did not access contents).
GitHub patched cloud within hours on March 4 and shipped patches March 10, public disclosure April 28. 88% of GHES instances were still vulnerable at disclosure🤯
Wiz used IDA MCP, an AI-augmented reverse engineering setup, to analyze GitHub’s compiled binaries and reconstruct internal protocols at a speed that wasn’t economical before.
Dig Deeper: Wiz technical writeup | GitHub’s response post (authored by GH CISO)
Cisco to acquire Astrix Security for $400M, betting on non-human identity
Cisco announced intent to acquire Astrix Security for roughly $400M, per Calcalist.
Founded in 2021 by Alon Jackson and Idan Gour (both Unit 8200), Astrix raised $85M total across rounds led by Menlo Ventures’ Anthology Fund (with Anthropic), Bessemer, CRV, Workday Ventures, and F2.
~5x return on $85M raised is pretty good for Astrix and sets the bar for other NHI platforms like Oasis, Token, and Entro etc.
Capabilities will fold into Cisco Identity Intelligence and extend into Duo and Secure Access, with detection signals piping into Splunk.
🔮 The Future of Security 🔮
AI Security
OpenAI ships passkey-only Advanced Account Security for ChatGPT and Codex
OpenAI rolled out opt-in Advanced Account Security for ChatGPT and Codex accounts, requiring passkeys or FIDO hardware keys and disabling password login, email, and SMS recovery.
Account recovery falls entirely on the user; OpenAI support cannot assist. Conversations are auto-excluded from training. Partnered with Yubico on discounted YubiKey bundles. Members of OpenAI’s Trusted Access for Cyber program must enable it by June 1. Not available for ChatGPT Enterprise or managed accounts yet.
More AI security news
Detection Engineering
Azure AD Graph Activity Logs land in Sentinel, closing a long-standing detection gap
Microsoft made the AADGraphActivityLogs table queryable in Azure Monitor and Sentinel, giving defenders visibility into the legacy Azure AD Graph API (graph.windows.net) for the first time. The modern graph.microsoft.com endpoint has had a logging table since 2023, but the deprecated legacy API stayed active and unlogged, a gap Cloudbrothers documented as the reason offensive tooling evaded detection. What’s now detectable:
AADInternals-based recon and persistence
Ping Castle assessment scans
Any custom tooling targeting the legacy endpoint
Historical Azure AD Graph activity once ingestion is enabled
A significant win for blue teams. The “use the deprecated API to evade logging” technique has been documented and used in the wild for years, and any tenant running detections was effectively blind to a chunk of legitimate-looking reconnaissance. The interesting question for red teamers: what’s the next evasion path now that this one is closed.
Expect new detection content from the usual Sentinel community shops within weeks.
Governance, Risk, and Compliance
Rippling launches Automated Compliance for SOC 2, brings in AJ Yawn
Rippling rolled out Rippling Automated Compliance on April 28, leveraging its position as the system of record for HR, IT, identity, and device management to auto-collect SOC 2 evidence. Available now for SOC 2 Type 1 and Type 2, with more frameworks on the way. Connected CPA firm and pen testing partners are wired into the audit workflow.
Compliance veteran AJ Yawn, founder of the GRC Engineering Club and one of the most credible voices in GRC engineering, also joined the team around the same time this was announced.
Rippling is right that GRC tools have been reporting layers on top of systems they don’t control, and being the underlying system flips the economics. Bringing Yawn in lends real practitioner credibility and Rippling has a true moat as they control much of the underlying surface that compliance probes for anyways. Rippling has a massive customer base so the upsell opp. is real.
Security Operations
CrowdStrike extends OverWatch managed threat hunting to Microsoft Defender
CrowdStrike launched Falcon OverWatch for Defender, bringing its threat hunting service to organizations running Microsoft Defender for endpoint without requiring an EDR rip-and-replace. The service layers continuous human-led hunting, adversary intelligence (CrowdStrike tracks 280+ tracked groups), and response guidance on top of Defender’s native detections. Builds on March’s Falcon Next-Gen SIEM for Defender integration.
Smart land-grab. Seems like CrowdStrike and MSFT are deepening their partnership which is ultimately, what’s best for both customer bases.
Interested in sponsoring TCP?
Sponsoring TCP not only helps me continue to bring you the latest in security innovation, but it also connects you to a dedicated audience of 20,000+ CISOs, practitioners, founders, and investors across 135+ countries 🌎
Bye for now 👋🏽
That’s all for this week… ¡Nos vemos la próxima semana!
Disclaimer
The insights, opinions, and analyses shared in The Cybersecurity Pulse are my own and do not represent the views or positions of my employer or any affiliated organizations. This newsletter is for informational purposes only and should not be construed as financial, legal, security, or investment advice.