📡 Cybersecurity Innovation Pulse #27: Shared Fate in GenAI; GUTSY's $51M Seed; Tradecraft Innovation; Has My Secret Leaked?; Automatic Attack Disruption and So Much More!
Covering Oct. 4th - Oct. 19th
Welcome to Issue 27 of the Cybersecurity Innovation Pulse! I'm Darwin Salazar, your compass to the dynamic world of cybersecurity innovation. Each week, I deliver the latest on product debuts, groundbreaking innovations, strategic collaborations, and other developments at the intersection of innovation and cybersecurity. Digging these updates? Subscribe and get the intel delivered straight to your digital doorstep, ensuring you're always in the loop 🚀
Intro 🫱🏼🫲🏽
Howdy! While there was no issue sent out last week, I still went back and made sure to cover all the most buzzworthy innovations across the space since our last issue. This means that this issue is jam-packed with a bunch of goodness ranging from new cutting-edge product features, open-source LLM security tools, and with the introduction of our new “Tradecraft Innovation” section, we also cover new attacker techniques. Oh, and I’m also working on my meme game. That said, grab a drink, sit back, and enjoy this week’s issue!
🛰️Industry Innovation 🛰️
Google Cloud Introduces Generative AI Indemnification to Safeguard Customers
In an industry-first, Google Cloud recently took a massive step towards a shared fate future with generative AI indemnification, moving away from the typical shared responsibility models where customers are often left to handle the legal ramifications tied to technology use. It’s also key to note that Google Cloud is pretty bullish on a shared fate future even for cybersecurity. These are the types of protections that cloud giants should have been providing customers from the outset, imo, especially for SMBs.
Anyways, this protection is particularly targeted at addressing legal uncertainties surrounding intellectual property (IP) that might arise when using any of Google's generative AI products. The indemnification comes in two parts:
Training Data Indemnity: This covers any allegations that Google’s use of training data for generative AI models infringes a third party’s intellectual property rights. It's a reassurance for customers, taking away the legal worries around the training data utilized in creating generative AI models.
Generated Output Indemnity: This is the second layer of protection, covering the output generated by customers using Google’s services. It applies to various products including Duet AI in Google Workspace and several Google Cloud services, ensuring customers are shielded from third-party intellectual property claims tied to generated content, provided they adhere to responsible AI practices.
This move by Google Cloud is about creating a legally sound playground for customers to innovate and utilize generative AI technology, wiping away some of the legal concerns customers may have while building with the generative AI suite.
Source: Google Cloud Blog
Gutsy: Notable $51M Seed Funding, Innovative Approach, Veteran Founders
The team behind Twistlock, now part of Palo Alto, recently came out of stealth with their startup called Gutsy, securing a hefty $51 million in seed funding. Gutsy aims to be team’s “security governance co-pilot” to revolutionize security governance through process mining.
Process mining is a data science technique used to analyze and monitor the processes within an organization. By examining the event logs, security findings, and other data points, process mining can, in theory, provide a clear picture of how different systems and workflows interact, identifying inefficiencies and areas for improvement. In the realm of cybersecurity, process mining can highlight security gaps and inconsistencies in real-time, enabling quicker responses to potential threats. Gutsy's approach leverages process mining to provide actionable insights, aiming to improve identity management, incident response, and vulnerability management within organizations. I like it. Let’s see what the execution looks like.
Source: SecurityWeek
NSA's Elitewolf: A Step Towards Secure OT and Critical Infrastructure
The NSA released a repository named Elitewolf, containing detection signatures and analytics for Industrial Control Systems (ICS) and other Operational Technology (OT) environments. Bravo to the NSA for open-sourcing this 👏🏽👏🏽👏🏽
Source: SecurityWeek
CISA Adds Ransomware Insights to KEV Catalog
CISA recently added a new column to their Known Exploitable Vulnerabilities (KEV) that identifies whether a vulnerability has been leveraged in a ransomware campaign. There are several reasons why this is a game changer, but most importantly, this will help security teams with remediation prioritization which has long been a pain point since not all critical and high severity vulns are exploitable or reachable.
Shameless plug, Monad recently added this column to the CISA KEV Enrichment connector which means users now get these insights directly to their security data lakes.
Source: CISA
Reality Defender Secures $15M to Combat Deepfakes
Reality Defender, a startup focusing on detecting deepfakes and other AI-generated content, has bagged $15 million in a Series A funding round led by DCVC and with contributions from Comcast, Ex/ante, Parameter Ventures, and Nat Friedman’s AI Grant. The funds will be used to expand the team and enhance its AI content detection models. Reality Defender provides an array of tools via an API and web app, capable of analyzing videos, audio, text, and images for AI-driven alterations.
Source: TechCrunch
CISA and NSA Shed Light on Identity and Access Management Challenges
CISA and NSA recently released a publication addressing IAM challenges faced by developers and technology manufacturers. Authored by the Enduring Security Framework (ESF), it's a cross-sector effort between the NSA and CISA to mitigate risks threatening critical infrastructure and national security. The guidance zeros in on technology gaps hindering the adoption of MFA and SSO technologies, providing actionable recommendations to both large and smaller organizations to enhance their IAM practices.
Source: CISA
🤺Tradecraft Innovation🤺
Protect AI Unleashes Trio of AI/ML Security Tools as Open Source
Protect AI has released three AI and Machine Learning security tools, NB Defense, ModelScan, and Rebuff as open source, and they’re now available on GitHub. Below is a breakdown of what each solution does:
NB Defense scans Jupyter Notebooks for a variety of vulnerabilities including leaked secrets, PII, CVE exposures, and more.
ModelScan scans Pytorch, Tensorflow, Keras, and other formats for model serialization attacks, such as credential theft, data poisoning, model poisoning, and privilege escalation.
Rebuff employs a self-hardening prompt injection detection framework to defend against prompt injection attacks.
Massive kudos to Protect AI for open-sourcing these tools. It’s definitely a game-changer for anyone working to secure AI/ML.
Source: Dark Reading
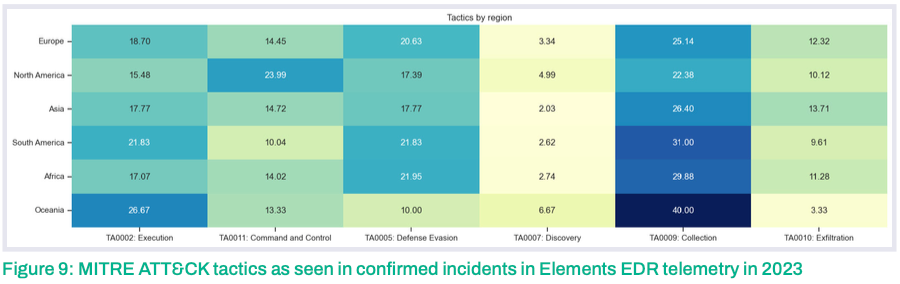
WithSecure’s Unveiling the Arsenal: Exploring Attacker Toolsets and Tactics
WithSecure recently came out with a research report that dives into attackers’ toolsets and tactics based on telemetry and insights collected from their Elements EDR solution. The report highlights different paths attackers use to achieve their objectives and includes a geographical breakdown. The report has nice graphics and maps to the MITRE ATT&CK matrix making it actionable for organizations to refine and test their defenses based on the findings from the report.
Source: WithSecure
Defending Against New Attack Vectors: SQL Server to Cloud Lateral Movement
Microsoft sheds light on a new attack vector where threat actors exploit SQL Server connections to maneuver laterally to cloud environments. Details and detection opportunities in the blog post below.
Source: Microsoft Security Blog
Unprecedented DDoS Attacks Leveraging HTTP/2 Zero-Day Vulnerability
The world recently witnessed a record-breaking Distributed Denial of Service (DDoS) attack, leveraging a zero-day vulnerability known as 'HTTP/2 Rapid Reset' in the HTTP/2 protocol. This attack, hitting an astonishing 398 million requests per second (RPS), overwhelmed servers and marked the largest DDoS attack in internet history. The 'HTTP/2 Rapid Reset' flaw, significant for multiplexing requests over a single TCP connection, was exploited to create concurrent streams that amplified the attack volume.
Disclosure of this vulnerability and the attack were brought to light by major tech entities like Cloudflare, Google, and Amazon Web Services (AWS).
Source: Packet Storm Security
Prompt Injection Vulnerability Explored in GPT-4 Vision
The newly introduced GPT-4 Vision brings a prompt injection vulnerability to light, where malicious actors can inject harmful data through images, bypassing text prompts and guardrails. This issue arises as GPT-4 can now read text within images, potentially acting on malicious instructions embedded therein. A worrying facet of this vulnerability is that text hidden in images, undetectable to the human eye, can still be recognized and acted upon by GPT-4, due to its adept Optical Character Recognition (OCR) capabilities, opening a new avenue for attacks on LLMs. This is particularly concerning for mission-critical apps that may rely on Open AI’s Vision capabilities.
Source: Roboflow Blog
🛸Product Innovation🛸
Microsoft Defender for Endpoint Advances with Automatic Attack Disruption
Microsoft has unveiled an insanely cutting-edge feature for Defender for Endpoint called Automatic Attack Disruption. I come across hundreds of new features and products every month but this one has to be in my top 3 for the year.
Automatic attack disruption uses signal across the Microsoft 365 Defender workloads (identities, endpoints, email, and software as a service [SaaS] apps) to disrupt advanced attacks with high confidence. - Microsoft Blog
Essentially, upon detecting an initial threat on a device, Microsoft not only neutralizes it but also immunizes all other devices within the organization against the attack. The official blog post has more details on the how and also includes a real-world example of when this feature helped thwart an attack against a medical research lab in August 2023.
Source: Microsoft Security Blog
Prisma Cloud Darwin Update Boosts DevSecOps Communication and Velocity
Prisma Cloud has rolled out the Darwin update to its DevSecOps software, enhancing the collaboration between security teams and developers. The update introduces six features like AppDNA visualization, a knowledge graph-based topology for security attack paths, and "fix in cloud" and "fix in code" remediation options.
These features aim at addressing vulnerabilities promptly and enhancing cloud security. The “securing code to cloud” play is clutch for organizations that want as little administrative overhead and silos between teams and solutions. I’m definitely a huge fan of the Darwin update 😀. Sorry, I had to.
Source: Palo Alto Networks
Wiz Introduces Google Workspace Support
Wiz has rolled out support for Google Workspace identity modeling as part of its Cloud Infrastructure Entitlement Management (CIEM) capabilities, providing Google Cloud customers with a tool to protect their cloud identities. This new feature offers visibility into Google Cloud entitlements, helps identify misconfigurations in Google Cloud and Google Workspace, and enables the proactive removal of attack paths to harden the environment.
Source: Wiz Blog
AWS Unveils PCI DSS v4.0 Compliance Guide
Amazon Web Services (AWS) has introduced the PCI DSS v4.0 on AWS Compliance Guide to assist customers in adhering to the Payment Card Industry Data Security Standard (PCI DSS) v4.0 when utilizing AWS services. The guide answers frequently asked questions and offers guidance on building PCI DSS-compliant applications. It covers the Shared Responsibility Model, AWS PCI DSS Level 1 Service Provider status, scoping cardholder data environment, and offers requirement-by-requirement guidance, aiding customers, compliance teams, and PCI Qualified Security Assessors in managing assessments of cloud applications. #Yuge
Source: AWS Security Blog
SailPoint Unveils Next-Gen Atlas & Identity Cloud
SailPoint has launched its SailPoint Atlas platform, a multi-tenant SaaS platform forming the core of SailPoint Identity Security Cloud, to enhance identity security operations for modern enterprises. This platform provides a range of services including rich identity context, access activity intelligence, and embedded AI, alongside features like extensibility, personalized insights & reporting, a robust data model, machine learning, connectivity, and event-driven orchestration. These offerings aim to improve business processes, access decisions, and enable a Zero-Trust security model.
Source: Forbes
CyberArk Amplifies Secure Cloud Access
CyberArk has updated its Secure Cloud Access solution, part of the CyberArk Identity Security Platform, to enhance cloud security. The new features include just-in-time access, identification of IAM misconfiguration risks in multi-cloud settings, context-based approval workflows for high-risk cloud service access, and extended regional data center coverage. These additions aim to reduce credential theft risks and excessive access while promoting secure multi-cloud deployments
Source: Help Net Security, VMblog
GitGuardian Introduces Novel Secret Management Service
GitGuardian has launched a service dubbed "Has My Secret Leaked" to address the challenges of managing software encryption keys and other secrets for enterprise security managers. This service provides a platform where a copy of the secret can be pasted into a query box, and the system reveals whether it has been spotted in any dark web or other public context.
Source: SiliconANGLE
Conclusion
That's all for this week! I hope you found this issue insightful. Your feedback shapes the future of this newsletter, so drop me a line on what resonated with you or what you'd like to see more of. If you believe others can benefit from these insights, share the love and encourage them to subscribe. Every week, I dive deep into a sea of headlines to curate the most pivotal stories in cybersecurity innovation just for you. Your continued support is a testament to the value this brings. Catch you in the next issue!