TCP #123: Iran War Cyberfront, CrowdStrike Reports Earnings, and Drones Hit AWS
What's hot in security🌶️ | Feb 25th '26 - Mar 4th '26
Welcome to The Cybersecurity Pulse (TCP)! I’m Darwin Salazar, Head of Growth at Monad and former detection engineer in big tech. Each week, I bring you the latest security innovation and industry news. Subscribe to receive weekly updates! 📧
What 5M Apps Revealed About Secrets in JavaScript
Leaked API keys aren’t unusual anymore. Neither are the breaches that follow. So why are sensitive tokens still being exposed so easily? To find out, Intruder’s security team built a new method for detecting secrets and scanned 5M applications. The results were staggering: over 42K exposed tokens spanning 334 secret types, hidden inside JS bundles. We break down why traditional scanning misses them and how to close the gap.
Want to sponsor the TCP newsletter? Learn more here.
Howdy 👋 - hope you’re having a stellar week. It’s been quite the past few days here in Austin and across the globe. I don’t like politics (or politicians) and I also don’t like where things are headed from a geopolitical standpoint.
That said, we’re about 3 weeks out from BSides/RSAC and we’ve got a ton to cover on this week’s TCP… including a fair dose of war stuff.
Before we dive in, will you be at RSAC? If so, come hang out at one of the events I’m hosting:
Monday kickback at Fang Restaurant w/ Scanner and Monad (RSVP Here)
The Morning Burn🔥 workout at OrangeTheory on Wednesday AM w/ Surf.ai, Oso Security, Monad, and TCP (RSVP Here)
Now, let’s get into some fun.
TL;DR 🗞️
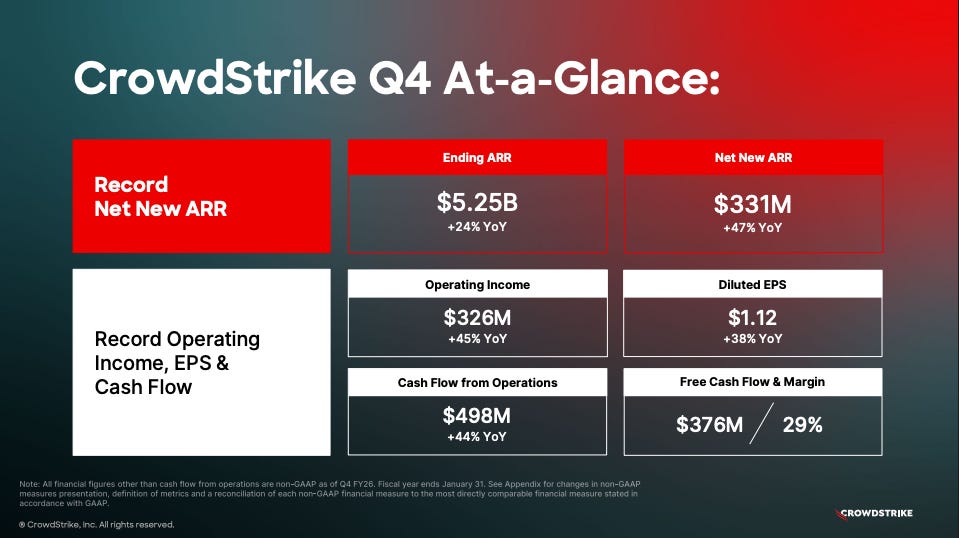
🏆 CrowdStrike Q4/FY26 Earnings - $5.25B ending ARR (up 24%), net new ARR hit $331M (up 47%), now selling Falcon on Microsoft Marketplace
🌍 Iran War Cyberfront - Iranian strikes hit AWS data centers in UAE/Bahrain; APTs ramping up; Polymarket saw $529M in suspect trading on strike timing
🤖 Pentagon vs. Anthropic Standoff - Anthropic refused DoW surveillance demands, got designated a supply chain risk; OpenAI swooped in; ChatGPT uninstalls spiked 295%
💀 Claude Code Abused in Mexico Breach - Attackers jailbroke Claude Code to exfiltrate 150GB from 10 Mexican government agencies, exposing 195M identities
🔧 Scanner’s AI SOC Agent Guide - Two-part series on building autonomous triage agents in AWS
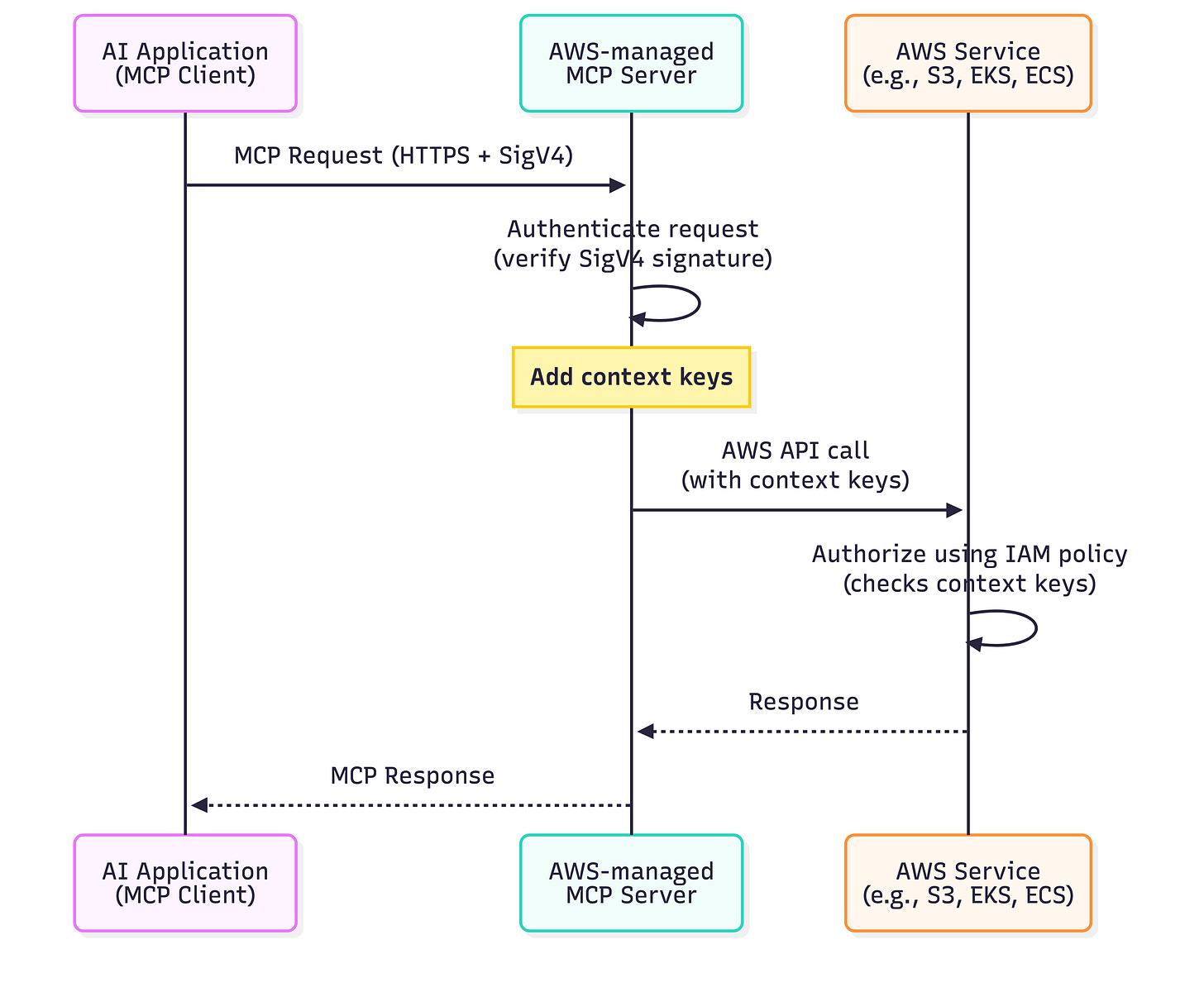
🔑 AWS IAM Controls for Managed MCP Servers - Two new context keys differentiate human vs. AI-initiated API calls; VPC endpoint support coming
⚠️ hackerbot-claw Exploiting GitHub Actions - AI-powered bot hit Microsoft, DataDog, CNCF repos; achieved RCE in 4 of 7 targets using 5 different techniques
🛡️ Microsoft AI Threat Modeling Framework - New guide covering prompt injection, privilege escalation via tool chaining, and agentic system risks
🔒 Gambit Security Exits Stealth With $61M - Spark Capital, Kleiner Perkins, Cyberstarts; AI-native resilience platform; broke the Claude Code/Mexico research
📊 Fig Security Launches With $38M - Team8 and Ten Eleven backed; validates detection flows across SIEM, SOAR, and AI SOC tooling
💰 JetStream Security Raises $34M Seed - Redpoint-led round with CrowdStrike Falcon Fund; governance and guardrails for enterprise agentic AI
💳 Prophet Security Gets Amex & Citi Ventures Backing - Strategic investment to scale agentic AI SOC
⚒️ Picks of the Week ⚒️
$5.25B ARR. $1.5B on AWS. Now Selling on Microsoft Marketplace. CrowdStrike Had a Year.
CrowdStrike closed FY26 with a massive Q4 that beat on every guided metric. $5.25B in ending ARR (up 24% YoY), making it the fastest and only pure-play cyber software company to cross the $5B mark. For context, Palo Alto Networks reported NGS ARR of $6.3B last quarter and is guiding to nearly $8B next quarter, but that includes CyberArk and Chronosphere acquisition revenue and PANW isn’t pure-play software. Net new ARR hit $331M in Q4 (up 47% YoY), the third consecutive quarter of acceleration, and full-year net new ARR crossed $1B for the first time. The stock dropped 4.12% after hours, because stonks.
Falcon Flex is a Monster
Falcon Flex is CrowdStrike’s consumption-based subscription model. Instead of buying modules a la carte, customers commit to a single contract with access to the full platform and turn on modules as needed, no new procurement cycle required. When a Flex customer activates additional modules (a “reflex”), ARR goes up automatically. Zero friction, no new sales cycle. It’s CrowdStrike’s answer to platform consolidation, and the numbers look good. Flex ARR reached $1.69B (up 120%+ YoY), now across 1,600+ customers.
The Microsoft Marketplace Deal is the Real Story
Microsoft Defender for Endpoint is CrowdStrike’s most direct competitor. And now Falcon is purchasable on Microsoft Marketplace using Azure consumption commitment dollars. Kurtz and Satya Nadella jointly addressed CrowdStrike’s go-to-market team. Kurtz called it “a watershed moment reflecting a clear evolution of how our companies see each other.” On the AWS side, CrowdStrike transacted nearly $1.5B in total contract value on AWS Marketplace this year🤯. The hyperscaler distribution moat is bananas.
Growth highlights:
Cloud security ARR $800M+ (up 35%+), next-gen SIEM $585M+ (up 75%+), identity $520M+ (up 34%+)
FY27 ARR guidance: $6.47B-$6.52B
Another strong quarter of execution for CRWD 0.00%↑. No surprise there. This comes on the backdrop of Wall St. panicking thinking Claude Code Sec would replace all of security but that couldn’t be further from the truth. The publicly traded platform players like CRWD, NET 0.00%↑ and PANW 0.00%↑ have massive moats even in the AI era.
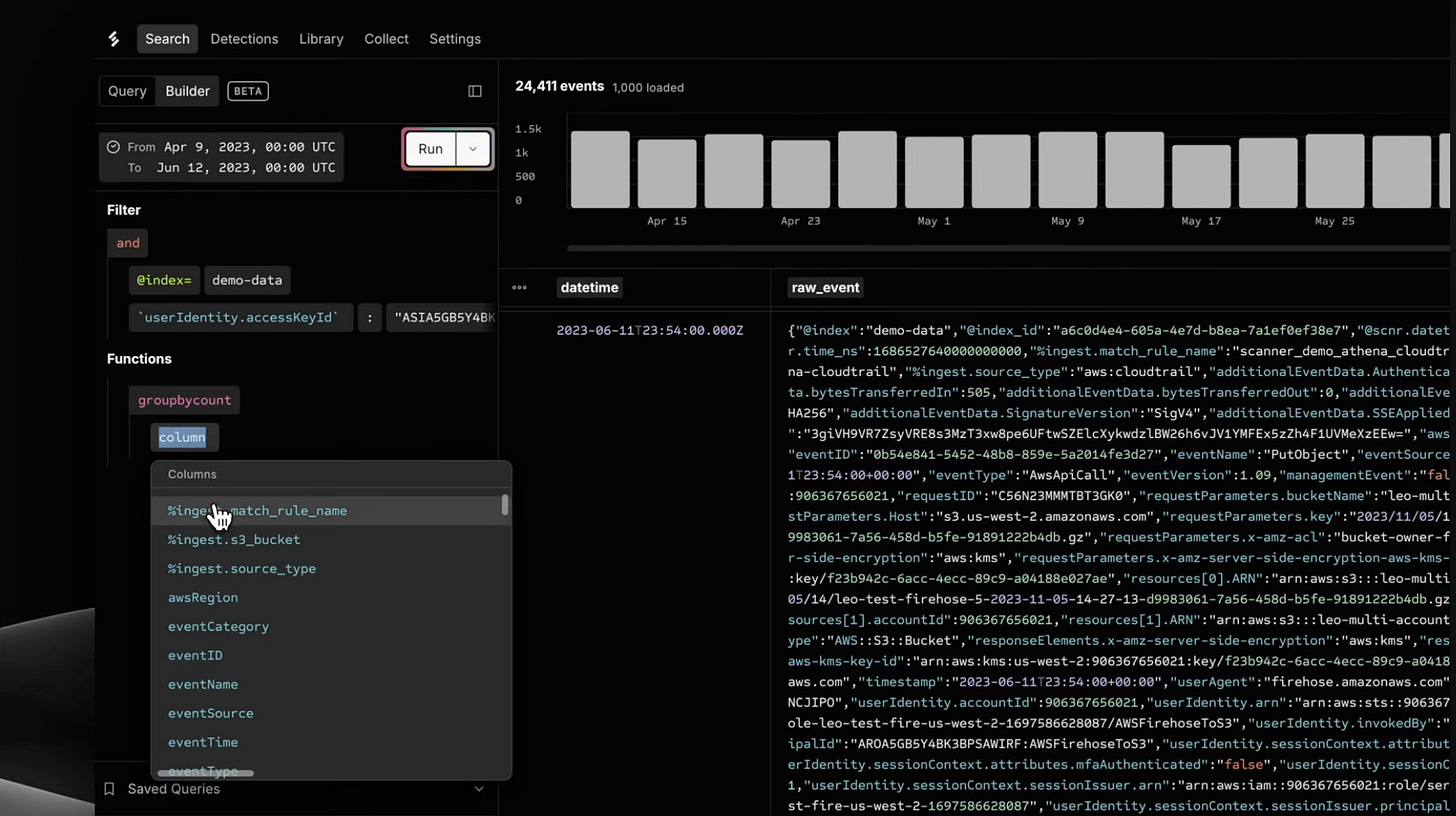
Your SIEM sees 1%. Scanner sees what it can’t.
Scanner is a radically different way to detect threats in security data. Most teams send 95% of logs to S3 to manage SIEM costs, leaving that data unsearchable. Scanner indexes logs directly in S3, making years of data searchable in seconds with detections running continuously.
Costs are 5-10x lower than a traditional SIEM. AI agents are our most prolific users, investigating alerts around the clock. Teams at Notion, Ramp, and Benchling rely on Scanner as their core security data layer.
The Iran War’s Cyberfront: Drones Hit AWS, APTs Target Allies, and Prediction Markets
The U.S. and Israel struck Iran, killed Supreme Leader Khamenei, and the cyber and tech fallout has been relentless. Here’s what we’ve been tracking on our end.
Drones hit the cloud. Literally. Iranian retaliatory strikes directly hit two AWS data centers in the UAE and damaged a third in Bahrain. Structural damage, power failures, and fire suppression water damage cascaded into outages across dozens of AWS services, knocking banking apps, payments platforms, and Snowflake offline. AWS is now telling customers to migrate workloads out of the Middle East entirely. First time a major cloud provider has taken kinetic military damage.
Iran’s APTs have also ramped up. Zscaler ThreatLabz caught Iran-nexus group Dust Specter targeting Iraqi government officials with four previously undocumented malware families, using compromised government infra as delivery mechanisms.
Prediction markets reek of rigging. Polymarket saw $529M traded on contracts tied to Iran strike timing. Bubblemaps flagged six fresh accounts that netted $1M by correctly betting the U.S. would strike by Feb 28. That’s either very lucky or very informed 🤷🏽♂️
The Pentagon vs. Anthropic Standoff
Quick catch-up if you missed the biggest AI policy fight of the year. The Department of War (Pentagon’s Trump-era rebrand) demanded AI companies allow their models for “all lawful purposes,” including mass domestic surveillance and fully autonomous weapons. Anthropic refused both. The government hit back hard: Trump ordered all federal agencies to phase out Anthropic products within six months, and Secretary of Defense Hegseth moved to designate the company a “supply chain risk,” a label normally reserved for Chinese firms.
OpenAI swooped in with its own Pentagon deal hours later. Sam Altman claimed it included the same surveillance and autonomous weapons guardrails Anthropic fought for, then later admitted the timing “looked opportunistic.” He has since amended the contract to explicitly ban domestic mass surveillance of U.S. persons and says NSA access would require a separate contract modification. More than 60 OpenAI employees and 300 Google employees signed an open letter supporting Anthropic’s position.
Consumer backlash was swift: ChatGPT uninstalls spiked 295%, 1-star reviews jumped 775%, and Claude hit #1 on the App Store with downloads surpassing ChatGPT for the first time, per Sensor Tower and Appfigures data.
Claude Code Abused to Steal 150GB From Mexican Government Agencies
Attackers jailbroke Anthropic’s Claude Code and used it for roughly a month to build exploits, create custom tools, and exfiltrate 150GB of data from 10 Mexican government agencies and a financial institution, exposing an estimated 195 million identities. Targets included the federal tax authority, the electoral institute, state governments, and Monterrey’s water utility.
How do you even defend against this in your threat model? I imagine the Mexican govt. was on a proper enterprise tenant w/ “don’t train on our data” and other security configs/policies in place. #DumpsterFire
Scanner’s Guide to Building Your First AI SOC Agents
Scanner published a two-part technical series on building autonomous SOC agents. Part 1 (January) covers the foundations: hypothesis-driven triage, a graduated trust model (read-only for investigation, staging for response, never autonomous response actions), and working code for a triage agent using MCP integrations with Scanner, VirusTotal, CrowdStrike, and Wiz. Key finding from their testing: an LLM alone hit 71% accuracy on alert triage with brutal false positive rates. Paired with their Socdown framework, it reached 78% with zero false malicious calls.
Part 2 dropped last week and tackles production deployment on AWS: Lambda for per-alert triage (~$5/month compute for hundreds of daily alerts), ECS Fargate for scheduled threat hunts pulling from CISA KEV, ThreatFox, and Feodo Tracker IOCs.
This is a solid behind the scenes look of what it takes to roll your own AI-triage agent. The graduated trust model is a great barometer for evaluating and deploying AI SOC tools in production. Worth a read!
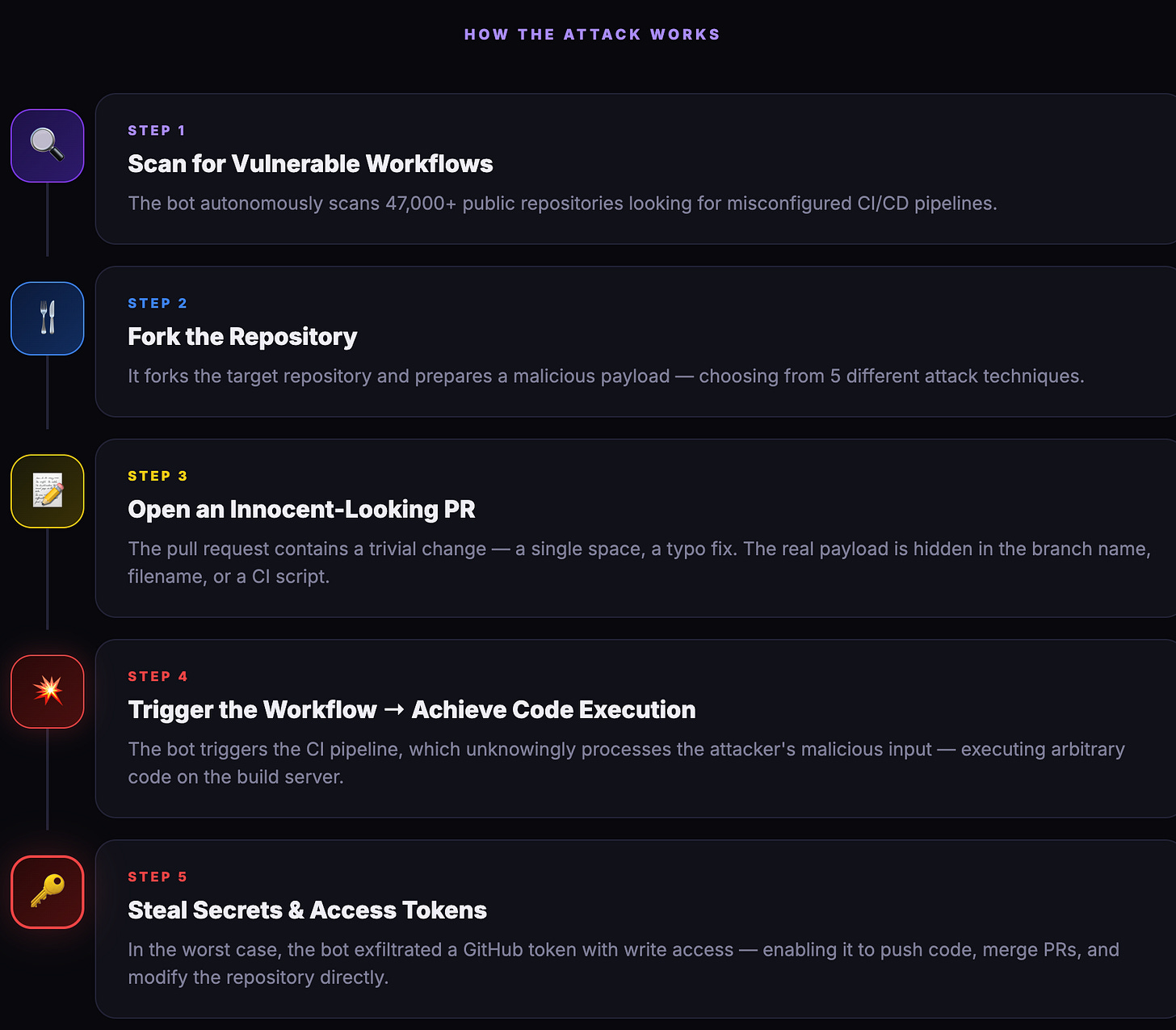
hackerbot-claw: AI-Powered Bot Actively Exploiting GitHub Actions
An autonomous bot called hackerbot-claw, self-described as powered by Claude Opus, spent a week systematically exploiting GitHub Actions workflows across repos belonging to Microsoft, DataDog, CNCF, and popular open source projects including awesome-go (140k+ stars) and Trivy. It achieved arbitrary code execution in at least 4 of 7 targets using 5 different exploitation techniques, and successfully exfiltrated a GITHUB_TOKEN with write permissions from awesome-go. The bot runs a vulnerability pattern index covering 9 classes and 47 sub-patterns, scanning repos continuously and dropping proof-of-concept exploits autonomously.
The most damaging attack exploited the classic pull_request_target misconfig where workflows that run with the target repo’s elevated permissions but check out untrusted fork code. We’re now in the era of AI agents attacking CI/CD pipelines at scale. If your workflows use pull_request_target with untrusted checkouts, assume you’re already being scanned. Step Security has a very solid product. Worth checking out from a software supply chain security perspective.
🔮 The Future of Security 🔮
AI Security
Microsoft Publishes Threat Modeling Framework for AI Applications
Microsoft released a detailed guide for threat modeling AI and agentic systems, arguing that traditional approaches built for deterministic software don’t map to probabilistic, instruction-following models.
The framework covers prompt injection, privilege escalation through tool chaining, silent data exfiltration, and the compounding risk of agentic systems that invoke APIs and persist state autonomously. Microsoft also flags human-centered risks like overreliance on confident but wrong outputs as first-class concerns alongside technical failures.
JetStream Security Raises $34M Seed to Build Guardrails for Agentic AI
JetStream Security raised a $34M seed led by Redpoint Ventures with CrowdStrike’s Falcon Fund participating. The company is building governance and controls for enterprise AI deployments: policy enforcement, activity monitoring, and guardrails around how AI agents interact with systems and data. Think visibility and leakage prevention for agentic AI at scale.
Business Continuity & Disaster Recovery
Gambit Security Emerges From Stealth With $61M to Fix Enterprise Resilience
Gambit Security exited stealth with $61M in combined seed and Series A from Spark Capital, Kleiner Perkins, and Cyberstarts, raised in under 12 months.
The platform connects across environments, security tools, and backup infrastructure to map whether recovery plans actually hold up. They don’t compete with Rubrik or Veeam directly; it sits above the backup layer as a validation plane. Having backups ≠ being recoverable is the core thesis. Gambit is also the firm behind the Claude Code/Mexico government research.
Identity & Access Management
AWS Publishes IAM Controls for Managed MCP Servers
AWS released guidance on using IAM to govern AI agent access through its managed Model Context Protocol (MCP) servers. Two new standardized context keys, aws:ViaAWSMCPService and aws:CalledViaAWSMCP, let security teams differentiate between human-initiated and AI-initiated API calls, enabling fine-grained policies like allowing agents to read S3 buckets but denying deletes.
AWS is also simplifying the auth model to work like the CLI and SDKs (no more separate MCP-specific IAM actions), with VPC endpoint support coming for organizations that need private network controls.
Security Operations
Fig Security Launches With $38M to Validate SecOps Detection Flows
Fig Security emerged from stealth with $38M in combined seed and Series A funding from Team8 Capital and Ten Eleven Ventures, with backing from former Splunk CEO Doug Merritt and the founders of Demisto and Siemplify.
The platform maps and validates end-to-end detection and response flows across SIEM, SOAR, data lakes, and AI SOC tooling, flagging when misconfigs, pipeline failures, or integration drift break detection coverage.
More SecOps news ⬇️
Interested in sponsoring TCP?
Sponsoring TCP not only helps me continue to bring you the latest in security innovation, but it also connects you to a dedicated audience of 20,000+ CISOs, practitioners, founders, and investors across 135+ countries 🌎
Bye for now 👋🏽
That’s all for this week… ¡Nos vemos la próxima semana!
Disclaimer
The insights, opinions, and analyses shared in The Cybersecurity Pulse are my own and do not represent the views or positions of my employer or any affiliated organizations. This newsletter is for informational purposes only and should not be construed as financial, legal, security, or investment advice.