TCP 130: Linux 0-day, Checkmarx leak, ShinyHunters double-hit, Google and Wiz go all in, and more
96GB dumped, CVSS 7.8 across 'every' linux distro, 17.7M records claimed, and three new SecOps agents from Google
Welcome to The Cybersecurity Pulse (TCP)! I’m Darwin Salazar, Head of Growth at Monad and former detection engineer in big tech. Each week, I bring you the latest security innovation and industry news. Subscribe to receive weekly updates! 📧
Ship Fast. Sleep Well.
The 2026 Identity Governance Playbook Is Here.
Speed and security don't have to be a tradeoff. The security teams ready for AI have automated what used to take weeks: access approvals, lifecycle management, unused access removal and built a unified identity graph ready for AI agents. Read Opal's 2026 report to learn how they did it.
Howdy 👋 - Hope you’re having a great week wherever you’re reading from!
This week has been quite eventful, literally. I had the opportunity to attend Intezer’s Nasdaq event in NYC and it was pretty insightful. F500 CISOs and security leaders shared how they’re thinking about AI, Mythos-level threats, how the buyer-vendor relationship has evolved, reporting up to the board and more. I have a full write-up coming out next Tuesday for this so I won’t spoil it all here. However, huge kudos to the Intezer GTM team for pulling off such a stellar event.
Aside from that, a quick heads up that DEF CON main stage Call for Papers, Labs, Workshops, Music and more closes today at 8PM ET. I think DC village CFPs closes a couple weeks later but always good to double check!
Also, a quick plug for this cool cost savings analysis feature that my team at Monad shipped.
Lastly, the past 2 TCP issues have gone out on Thursdays. We’ll be back to our regularly scheduled programming next Wednesday.
Cool, let’s dive in!
TL;DR ✏️
🩸 Checkmarx dump hits dark web — Lapsus$ posts 96GB archive after TeamPCP pivoted from Trivy → Checkmarx GitHub; 30-day persistence despite cred revocation
☁️ Google Cloud Next ‘26 ships agent governance — Three new SecOps agents, Wiz scanning all the things, Gemini Enterprise Agent Platform, Q1 earnings smoked
🐧 Copy Fail roots every Linux since 2017 — 732-byte Python script, CVSS 7.8, container escape primitive; not as critical as alarmist would have you think
🩺 ShinyHunters claims Medtronic and Carnival — 9M+ Medtronic records, 8.7M Carnival/Holland America loyalty records; both vectors still undisclosed
📊 Cyber insurance data is the real CISO ammo — Misconfigured MFA = 26% of losses, ransomware = 90% of total loss from 12% of claims. Industry needs more 3rd party data like this
💎 Opal's 2026 Identity Governance Report — Auto-granted access goes unused 50% of the time, NHIs outnumber humans 5:1, and 72% of CISOs say authz is their biggest AI blocker
🤖 Amazon CISO details RuleForge detection-rule pipeline — Bedrock generator agent proposes rules, separate judge model scores sensitivity vs specificity, MadPot honeypots validate before merge
Plus: Copperhelm exits stealth with $7M, Sublime Security goes 100% channel-led, and Silverfort acquires Fabrix Security ($8M raised to date) and more. 👇
⚒️ Picks of the Week ⚒️
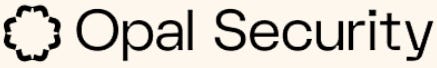
Checkmarx debacle: AppSec vendor caught in the Trivy/TeamPCP supply chain blast radius
Checkmarx (the AppSec vendor who markets itself as covering 40% of the Fortune 100, including Apple, Salesforce, Walmart, Visa, Citigroup, Ford, Siemens, Airbus, Adidas, and SAP) confirmed that Lapsus$ dumped a 96GB archive of its data (source code, employee database, API keys, MongoDB and MySQL creds) on dark web and clearnet portals.
The access vector: stolen creds from the March 23 Trivy supply-chain compromise attributed to TeamPCP, which gave attackers the keys into Checkmarx’s GitHub.
Timeline
Late Feb: TeamPCP compromises Trivy (Aqua Security’s open source vuln scanner)
March 16: Credential-stealing malware injected into Trivy, harvesting CI/CD secrets, cloud creds, SSH keys, and K8s configs from downstream users
March 23: Attackers use stolen Trivy creds to access Checkmarx GitHub
March 30: Data exfil from Checkmarx GitHub
April 22: Despite cred revocation and outbound blocks, attackers come back and poison the KICS Docker image, two VS Code/Open VSX extensions, and a GitHub Actions workflow
Late April: Lapsus$ lists Checkmarx on its leak site and dumps the archive
Blast radius
Same campaign also briefly compromised the Bitwarden CLI npm package (@bitwarden/cli 2026.4.0), live for ~90 minutes, hoovering AWS keys, GitHub tokens, and SSH creds. Bitwarden has 10M+ users, 50K+ business customers. AI startup Mercor also got pulled in via the related LiteLLM compromise; Lapsus$ offered 4TB including 939GB of Mercor source code for sale.
This is the X-factor with software supply chain compromises. There’s a super long tail of downstream impact which may last months to years.
Google Cloud Next: Wiz everywhere, agents for everything, and stellar Q1 ‘26 Performance
Google Cloud Next ‘26 came with a slew of security updates: three new SecOps agents, Wiz sprawling across every rival cloud and agent platform, and a new Gemini Enterprise Agent Platform with governance bolted on.
SecOps agents
The existing Triage and Investigation agent (which Google says chewed through 5M+ alerts last year, taking 30-min triage down to 60 seconds) gets three new siblings in preview:
Threat Hunting agent to chase novel TTPs and stealthy behavior
Detection Engineering agent to find detection gaps and write rules for them
Third-Party Context agent to pull external context into analyst workflows
Remote MCP server support hit GA, dark web intel went into preview in Google Threat Intelligence (Google claims 98% accuracy on millions of daily events, take that with the usual grain of salt), and Darktrace, Gigamon, and SAP join as new partner integrations.
Wiz securing all the things, everywhere
Wiz now scans Databricks and the agent stacks of basically every competitor: AWS AgentCore, Azure Copilot Studio, Salesforce Agentforce, plus Google’s own Gemini platform. Apigee, Cloudflare AI Security for Apps, and Vercel got integrations too.
New AI-SDLC capabilities: a Lovable integration that runs Wiz scans inside the vibe-coding platform, inline AI security hooks for IDEs and agent workflows that scan prompts and generated code pre-commit, and a dynamic AI-BOM to surface shadow AI tools across an environment.
Agent identity, fraud, Chrome
Gemini Enterprise Agent Platform ships with Agent Identity (cryptographic IDs, scoped delegation, audit trails per action), Agent Gateway (policy enforcement aware of MCP and A2A, plus prompt injection, tool poisoning, and data leakage protections), and Model Armor for runtime model/agent protection now integrating with Agent Gateway, Agent Runtime, and LangChain. reCAPTCHA got rebranded to Google Cloud Fraud Defense (GA), with human/bot/agent distinction coming in preview. Chrome Enterprise gets an AI-aware threat detection extension plus shadow AI reporting for unsanctioned web AI apps.
Also key to note that GOOGL 0.00%↑ absolutely smoked Q1 2026 earnings and I’d imagine Wiz will be a great add-on to their bottom line. Excited to see how it all plays out!
Copy Fail (CVE-2026-31431): one logic bug, every Linux distro since 2017
Researchers at Theori/Xint disclosed Copy Fail, a Linux kernel LPE (CVSS 7.8) that lets an unprivileged local user write 4 controlled bytes into the page cache of any readable file and pop a root shell via a 732-byte Python script that works unmodified across Ubuntu, Amazon Linux, RHEL, and SUSE. The bug is a logic flaw in algif_aead introduced by a 2017 in-place optimization commit, chained through AF_ALG and splice().
Critically, it’s not remotely exploitable by itself, but the same primitive crosses container and tenant boundaries via the shared page cache, which makes it serious for K8s nodes, CI runners (GitHub Actions self-hosted, GitLab, Jenkins), shell-as-a-service hosts, and any SaaS running tenant code. Theori/Xint surfaced it with their AI code-auditing tool and is using the disclosure page as a product showcase, so calibrate the marketing accordingly, but the bug itself is real and the PoC is public on GitHub.
Where to follow: the copy.fail landing page for the technical writeup and guidance on how to patch, the Theori GitHub issue tracker for ongoing distro confirmations, and your distro’s advisory page (Ubuntu, RHEL, SUSE, Amazon Linux, Debian).
ShinyHunters on a tear: Medtronic and Carnival both hit
ShinyHunters claimed two big names back to back this week: medical device giant Medtronic and the world’s largest cruise operator, Carnival Corporation.
Medtronic
Medtronic confirmed a data security incident affecting corporate IT after ShinyHunters listed it on its leak site in mid-April, claiming 9M+ records of personal info plus piles of internal corporate data. Medtronic has not validated the numbers and stresses that hospital networks running its devices are managed independently and were not exposed. ShinyHunters set a ransom deadline, then pulled the listing, which usually signals either negotiation or whatever face-saving move keeps the leak tab clean.
Carnival
Two days later, Have I Been Pwned flagged what it described as 8.7M records (with 7.5M unique email addresses) tied to the Mariner Society loyalty program run by Holland America, a Carnival subsidiary. Exposed fields: names, DOBs, genders, and membership status. Carnival’s framing: a phishing attack against a single user account, scope still being assessed. ShinyHunters posted on its leak site that “the company failed to reach an agreement with us despite our incredible patience,” adding “they don’t care.”
How did they get in?
Honestly, nobody’s saying. Medtronic’s disclosure is vague enough to drive a truck through (”an unauthorized party accessed certain internal systems”). Carnival’s only attributed vector is a single phished user account, which doesn’t square with terabytes of data unless that account had way more access than it should have. Neither side has named a SaaS platform, an initial access broker, or any IOCs
Cyber insurance data gives CISOs new ammo for budget talks
Misconfigured MFA drives more financial loss than any other single control failure, and ransomware drives 90% of total loss despite being only 12% of claims. The industry needs more of this kind of empirical claims data; vendor “state of X” reports don’t cut it for CISOs trying to justify budget against actual loss attribution.
New analysis from cyber insurer Resilience, drawn from its manufacturing claims portfolio (March 2021 to February 2026) and synthesized with IBM X-Force and KELA data. Misconfigured MFA accounted for 26% of losses, software vuln exploits 13%, and transfer fraud plus BEC tied to phishing and credential theft made up 30% of claims.
More insurers and ISACs should be publishing data like this. Claims data beats survey-based findings or vendor-funded research every time.
🔮 The Future of Security 🔮
Application Security
Wiz Code Week recap: visibility, IDE guardrails, and CI/CD as a first-class asset
Wiz ran Code Week in parallel with Google Cloud Next. Code Week is where they release a bunch of dev and AppSec-related features and announcements. This time around, they launched an AI-BOM that auto-inventories AI frameworks, models, and IDE extensions (Gemini Code Assist, Copilot, Cursor), plus an IaC Inventory that maps code-to-cloud blast radius.
New Wiz Code plugins for Claude Code and Cursor embed pre-commit hooks for hardcoded secrets, IaC misconfigs, and vulns, with new SAST rules mapped to the OWASP Top 10 for LLM and Agentic Applications.
Pipeline-side, Wiz now models CI/CD as first-class assets on its Security Graph, surfacing dangerous trigger configs, excessive perms, and prompt injection risks from AI agents, plus a CI-BOM for third-party action inventory.
Cloud Security
Copperhelm exits stealth with $7M for agentic cloud security platform
Copperhelm emerged from stealth with $7M in seed led by TLV Partners (with toDay Ventures, ICON, and SaaS Ventures Israel), pitching AI agents that autonomously monitor cloud environments, investigate threats, and execute remediation in real time while keeping humans in control.
Auto-remediation is the next frontier. Dozens of vendors going after it meanwhile security leaders remain skeptical/hesitant for the more critical stuff. Let’s see.
Email Security
Sublime Security goes 100% channel-led with new partner program
Sublime Security launched a formal channel partner program and is now operating as a 100% channel-led company.
Core elements of a partner-first GTM motion are recurring margins with deal protection, dedicated partner sales managers and SEs, technical enablement and accreditation, and co-marketing support. Wiz did the same and I covered it here. Channel-led sales is cool because some MSSPs and VARs have been around for decades and know where the bodies are buried regarding legacy, clunky tech and can accelerate displacement.
Identity and Access Management
Silverfort acquires Fabrix Security to add AI-native runtime access decisioning
Silverfort acquired Fabrix Security, an AI-native identity security startup founded in 2024, for an undisclosed price.
Fabrix had raised $8M to date. The product runs an identity knowledge graph paired with AI agents that handle authorization decisions, just-in-time access requests, and lifecycle management for human, non-human, and agentic identities (service accounts, API keys, bots, AI agents).
Vulnerability Management
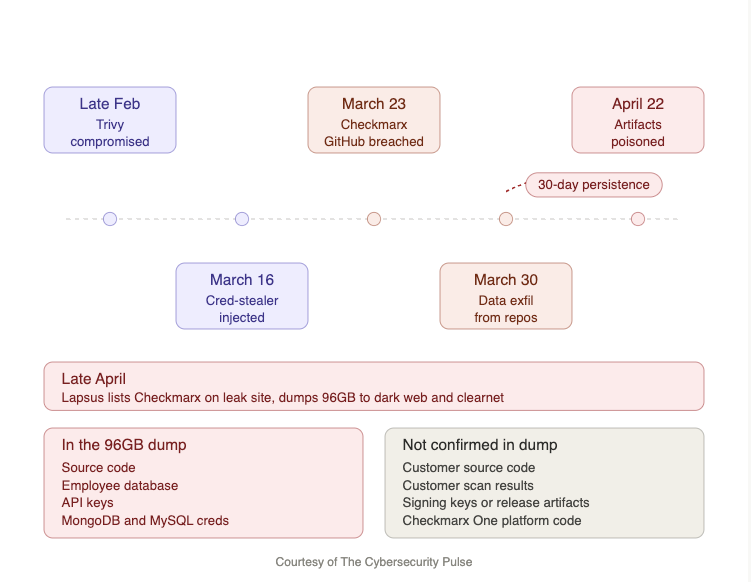
Amazon’s RuleForge: agentic AI generates production detection rules
Amazon CISO, CJ Moses recently wrote a blog about RuleForge, an internal agentic AI system that turns CVE proof-of-concept exploits into production-ready detection rules 336% faster than manual analyst workflows, with humans in the loop for final approval.
Architecture: a generation agent on AWS Fargate + Bedrock proposes multiple candidate rules in parallel; a separate judge model scores each on sensitivity (will this miss exploits?) and specificity (does it target the vuln or a correlated feature?).
Rules then run through synthetic testing and validation against MadPot honeypot traffic before code review.
The separation of generation from evaluation reduced false positives by 67% while preserving true positives, and Amazon credits negative-phrased prompts (”what’s the probability this rule fails?”) for better LLM calibration on security tasks.
This is one of the more honest hyperscaler writeups on applied AI for security stuff, and the architectural lessons (judge != generator, decompose the workflow, keep humans gating prod) are directly transferable to anyone building internal AI-based security tooling.
More vulnerability management news:
HackerOne Launches h1 Validation as AI Drives a Surge in Vulnerability Discovery
Rilian Raises $17.5 Million for AI-Native Security Orchestration
Interested in sponsoring TCP?
Sponsoring TCP not only helps me continue to bring you the latest in security innovation, but it also connects you to a dedicated audience of 20,000+ CISOs, practitioners, founders, and investors across 135+ countries 🌎
Bye for now 👋🏽
That’s all for this week… ¡Nos vemos la próxima semana!
Disclaimer
The insights, opinions, and analyses shared in The Cybersecurity Pulse are my own and do not represent the views or positions of my employer or any affiliated organizations. This newsletter is for informational purposes only and should not be construed as financial, legal, security, or investment advice.