The Dust Has Settled: Top Takeaways from RSAC & BSidesSF 2026
Build vs. buy, decoupled SOCs, MCP, and the builder mindset.
Welcome to The Cybersecurity Pulse (TCP)! I’m Darwin Salazar, Head of Growth at Monad and former detection engineer in big tech. Each week, I bring you the latest security innovation and industry news. Subscribe to receive weekly updates! 📧
Introducing the AI Security Platform Built on Data Security
AI adoption is exploding. But most security tools still can’t see what data AI is touching.
Varonis Atlas is designed to secure AI across the entire AI lifecycle, with data context built in. From visibility to runtime protection to governance, Atlas can secure everything you build and run with AI in one platform.
Though I’m still recovering from a 9-day conference stretch, this was easily my favorite BSidesSF + RSAC week. The energy was on point. I had 100+ conversations with security leaders on what they’re most excited about, biggest pain points, you name it. After RSAC, I ended up traveling 15 hours to another security conference where I presented on Saturday (more on that in a separate post ;)
It’s interesting because I wear multiple hats at conferences. I run this newsletter, so I’m always watching the emerging landscape from tradecraft to threats, tooling and capabilities, and how security leaders are future-proofing their teams and environments.
I’m also Head of Growth at Monad, so I do sales, marketing, and a bit of product management. If I learn that you have pain points Monad can solve, I will gladly pitch you on Monad and tell you about all the great stuff we’re up to. And at my core, I’m a security practitioner who still loves nerding out on how teams are staying current and how my previous crafts of detection engineering and cloud security continue to evolve.
That said, this post is an amalgamation and distillation of my biggest takeaways from the con from a holistic standpoint. Not my typical announcements roundup. That will come on Thursday!
Build vs. Buy is Shifting
In recent years, Build vs. Buy has become even more of a hot topic. The continual improvement of LLMs and agentic development has seriously lowered the barrier for entry. People are obviously all over the spectrum on this debate, but I feel like more people are leaning towards “Build” on certain categories than ever.
This was a main topic on the BSidesSF panel w/ security leaders from Anthropic, OpenAI, Perplexity, and Cursor. Here’s what stuck w/ me most after synthesizing a bunch of takes on this topic last week:
The gap between MVP and “production-ready” is where things get ugly. It varies by application, use case, and criticality, but that middle stretch is always messy.
Shipping it is only the beginning. Even after something is production-ready, you still have to staff for maintenance and scalability.
Some problems are just too hairy to own. Sometimes it makes more sense to pay someone else and hand off the problem entirely.
Do you want to be the one on-call when the thing you built breaks at 2am? - Jackie Bow, Detection & Response @ Anthropic
Midmarket Security Is Quietly Overconfident — And the Numbers Prove It
94% of midmarket security leaders say they can catch critical risks before attackers do. But 51% admit a zero-day would take a week to assess. Something doesn't add up. Intruder surveyed 500+ security decision-makers at companies with 400–6,000 employees to get the real picture of how teams are coping with growing digital estates, shrinking exploitation windows, and tooling built for enterprise budgets.
People Are Building Really Cool Things with AI
I had a few convos with security leaders including some at F500s who are super AI-pilled. We’re talking dedicated homegrown agents and skills for dozens of different security functions, mostly handling initial triage and investigations all the way through recommending remediation paths.
I also spoke with a leader who built a living, digital twin of their entire environment. If an AWS asset config gets changed, the digital twin gets updated. If a new admin account is spun up in Okta, the digital twin records it. Now, this person is an anomaly and pretty forward-thinking, but I think more and more people will continue to get creative with AI for security in meaningful ways. The ones who think outside the box, own the future, as always.
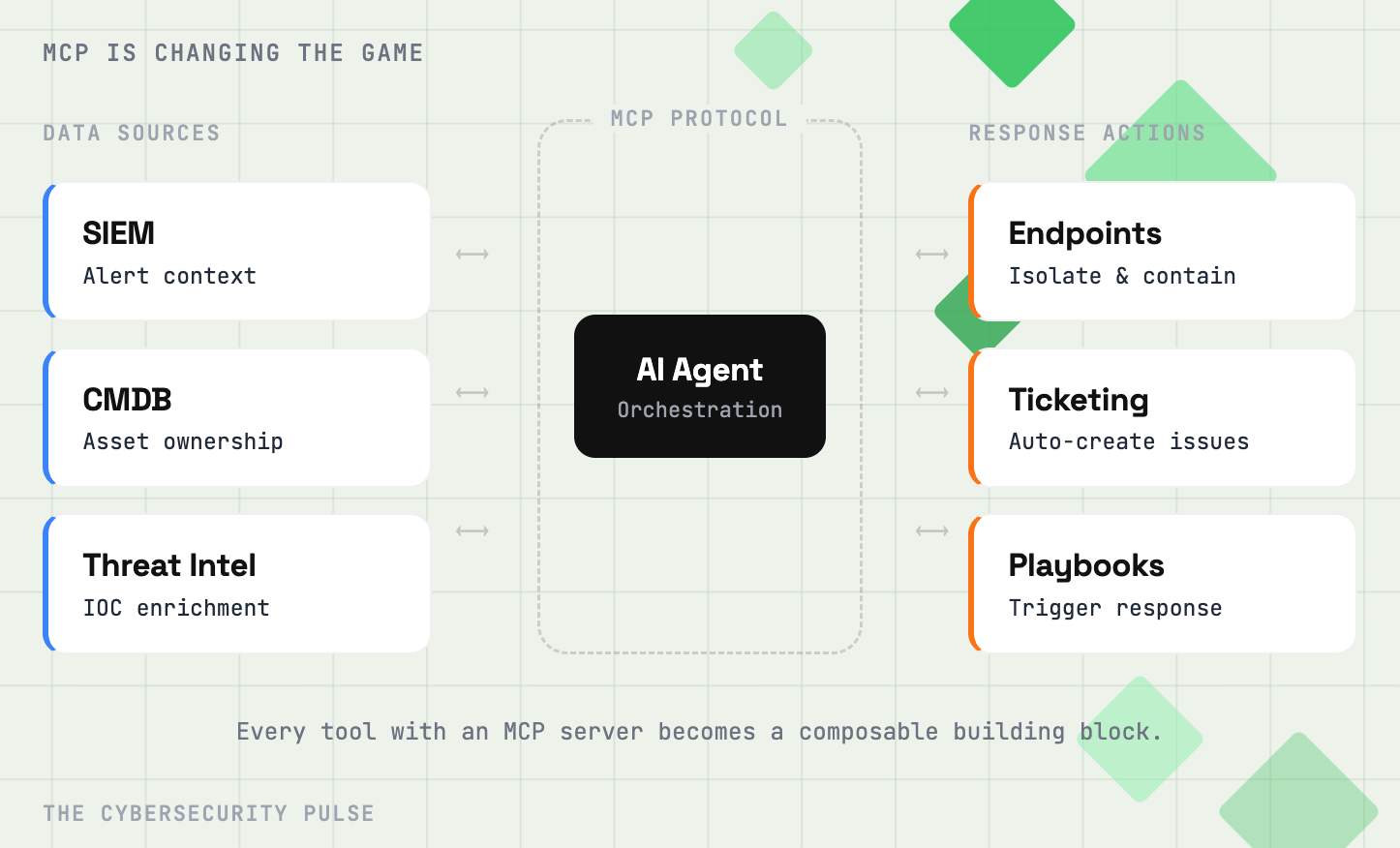
MCP is Changing the Game
Model Context Protocol (MCP) has played a massive role in modernizing security workflows. One leader I spoke with even said he won’t consider a new vendor if they don’t have MCP capabilities. I don’t agree with his take as I think MCP eats a lot of tokens.
But it does makes sense when you look at what it unlocks. Security teams are using MCP to give AI agents direct access to their tools. Think an AI assistant that can pull alert context from your SIEM, query your CMDB for asset ownership, and check your threat intel platform for IOC enrichment, all in a single investigation flow. Teams are also building MCP-enabled agents that can take action like isolating endpoints, creating tickets, or kicking off response playbooks based on findings.
It’s basically turning every security tool with an MCP server into a composable building block that AI can orchestrate across.
The security data lake for AI agents
Scanner is an agentic security data lake to investigate alerts, hunt threats, and respond to incidents. It indexes logs directly in S3, making years of data searchable in seconds. Scanner scales up when needed and scales to zero after, so you pay for answers, not idle compute. Open-source agents help you get started fast.
Decoupled Architectures for Security Operations
This goes hand in hand with the previous takeaway. More and more security leaders are considering a decoupled security architecture. Security data needs to live in more places than ever, especially with teams gaining more appetite to augment their tooling with homegrown capabilities. Recent breakthroughs are enabling teams to keep telemetry in ultra cost-effective, highly performant storage layers (Scanner.dev being a prime example) while data pipeline players like Monad have pretty much been the trojan horse enabling security teams to gain back control of how and where they route their data, with added benefits like enrichments and transformations that make data AI-ready.
I also heard more rumblings around federated search and how AI agents are good at querying data at the source for investigative work. The dust has yet to settle here but it’s clear that most security leaders are redrawing their SOC architectures, and there are a lot of emerging approaches and tooling to choose from. As someone who worked closely with Fortune 500 teams on detection engineering and response while at Accenture, this is a feel-good story. Security teams are breaking out of vendor lock-in and rebuilding their stacks with composable, best-of-breed solutions.
I’d say that after a long, hard-fought battle, SIEMs are no longer the one-stop shop for security analytics, response, and investigations. MCP, data lakes, data pipelines, triage agents etc. have disrupted the SIEMs moat. What comes next?
Talent and Upskilling
Security leaders are thinking hard about how to keep their teams at the forefront, not just of threats, but of evolving capabilities and tooling. They’re encouraging their people to adopt a builder mindset and go wider.
The world is changing fast. The ones who lean into the hacker and builder mindset will excel.
Honorable Mentions
Attack velocity + volume: Bad guys are using AI to find 0-days, exploit unpatched systems, and scale their campaigns. Defenders are cognizant of this and while there’s not an impending sense of doom, people are feeling the heat.
Agentic AI Identity: Still the wild west. No clear winner or winning approach, imo but we’re getting closer.
AI Pen Testing: Lots of funding and hype around it. I think it’s a space at risk if frontier model shops really wanted to go after it. Regardless, there’s a massive need for AI pen testing in validating vulns, securing new attack surface, and ensuring secure code and apps. This was a part of the security cycle that was painfully manual and having continual coverage here is a big upgrade.
Data Security: Scorching hot space and a top concern. Agentic AI is creating entirely new data access patterns that most teams aren’t equipped to govern yet. When your AI agents can autonomously query databases, pull documents, and chain API calls together, the blast radius of a misconfigured permission or over-scoped identity gets a lot bigger. Lots of energy here, and rightfully so.
Securing AI Code Gen Output and Agent Usage: Velocity and volume are big concerns, along with non-devs building small scripts to automate tasks. No clear winner here though the incumbents like Semgrep, Snyk, OX, etc. are shipping capabilities to keep up with the madness.
Software Supply Chain Security: Software Supply Chain Security: This one keeps getting scarier and giving me whiplash. March alone gave us the TeamPCP cascading campaign that started with compromising Aqua’s Trivy scanner, spread to Checkmarx KICS, and then used stolen CI/CD credentials to poison LiteLLM on PyPI (a library present in 36% of cloud environments according to Wiz). One compromised security tool turned into five compromised ecosystems in under a week.
And then literally today, Axios got hit with a hijacked maintainer account pushing a RAT through poisoned npm releases to a package with 100M+ weekly downloads. The window was only a couple hours but the blast radius is wild.
Scary pattern. Recommend checking these blogs out if you’re responding to these attacks:
The dust has settled on BSidesSF and RSAC 2026, but there is still SO much in flux for security teams. So in that sense, the dust may never for security teams. Just have to keep operating through the chaos which is easier when you have strong leadership + culture. Fun time to be in security.
I’ve still got a lot more to share. On Thursday, I’ll drop Part II covering the biggest announcements, my favorite events, and the overall vibes from the week etc. Stay tuned!
Interested in sponsoring TCP?
Sponsoring TCP not only helps me continue to bring you the latest in security innovation, but it also connects you to a dedicated audience of 20,000+ CISOs, practitioners, founders, and investors across 135+ countries 🌎