TCP #124: Security's Biggest Founders Return, AI Is Guarding Its Own Henhouse, and A Wiper Hits Healthcare
What's hot in security🌶️ | Mar 4th '26 - Mar 12th '26
Welcome to The Cybersecurity Pulse (TCP)! I’m Darwin Salazar, Head of Growth at Monad and former detection engineer in big tech. Each week, I bring you the latest security innovation and industry news. Subscribe to receive weekly updates! 📧
How Snyk Deploys AI Agents to Catch What Legacy Email Defenses Miss
Email threats are evolving faster than legacy defenses can keep up. Join Snyk and Sublime Security for a live webinar to see how Sublime’s AI agents detect, investigate, and stop attacks in minutes. See how Snyk uses Sublime’s Autonomous Detection Engineer (ADÉ) and Autonomous Security Analyst (ASA) to analyze missed threats, generate detections, and deploy new coverage at attacker speed.
Howdy 👋 - hope you’re having a stellar week. If you’re on the GTM side then you’re probably under the gun headed into RSAC and if you’re on the hands-on keyboard or leadership side of security… well then, you’re always under the gun. That said, make sure you’re touching grass + making time for yourself and family!
Before diving into anything security-related, I wanted to give a shout out to the Dominican Republic baseball team who is 4-0 in the World Baseball Classic and absolutely crushing it this year.
This is also a good opportunity to announce that I’ll be giving my first technical talk in 3 years in Dominican Republic later this month at HackConRD 🇩🇴. The talk is titled “Your detections are only as good as your data, aqui te enseño como resolver eso”… think Monad x MSFT Sentinel in Spanish. TCP is also sponsoring the con. More on that in coming weeks :)
Cool. Next personal note, I’ll be at BSidesSF/RSAC and it’s shaping out to be a super stacked week. If you’ll be in town and wanna meet, shoot me a DM here or on LIN ☕
I also highly recommend registering for our happy hour with our friends, Scanner.dev and coming to The Morning Burn workout at Orangetheory 🍊🔥 with our friends at Oso Security and Surf.ai… We may have a few surprises in store.
One more thing before news. We all know that traditional AppSec can’t keep up with AI code velocity and a structural shift is needed. Yes, better scanning + prioritization, but also moving security to where the most significant chokepoint for security is, and that’s at the design + architectural phase. Product security isn’t new but it’s mostly been IoT/OT companies who have adopted it up until recent years. I recently did a deep dive on this space and came away impressed by a vendor (Clover Security) who is tackling this in a such an eloquent fashion. Highly recommend carving time out to read here if you touch ProdSec or AppSec in any capacity.
Now, for the news!
TL;DR 🗞️
🩺 Iran-Linked Wiper Attack Devastates Stryker — Handala claims 200K+ systems wiped, 50TB exfiltrated from the $22.6B medtech giant across 79 countries.
🐔 When the Code Generator Is Also the Code Auditor — OpenAI + Claude double down on code scanning but who watches the henhouse?
📐 The AppSec Model Was Built for a World That’s Disappearing — Our deep dive on why security needs to shift to the design and architecture phase
🎯 What Actually Separates Effective CISOs — Lenny Zeltser and Aimee Cardwell on tenure, trust, burnout, and why most CISOs advise when they should act.
🎙️ [un]prompted Con Now Lives in NotebookLM — Every talk and slide deck from the AI security conference, searchable and podcast-ready.
🏗️ Mandia’s Armadin Raises Record $189.9M — Largest seed/Series A in cybersecurity history for AI-driven attack simulation.
📊 Scanner Raises $22M Series A Led by Sequoia — Super fast search across years of log data in object storage; AI agents now its most active users.
⚔️ AI as Tradecraft: How Threat Actors Operationalize AI — Microsoft breaks down how adversaries are integrating AI into real-world attack operations.
🛡️ Governing MCP Servers with an AI Gateway in Azure — Hands-on lab for security engineers locking down MCP server access in Azure.
⚡ Kai Emerges with $125M for Agentic Security — Claroty co-founder’s new play to unify IT and OT security ops at machine speed.
🔇 Jazz Exits Stealth with $61M — AI-powered DLP that understands intent and context; cut one customer’s daily alerts to 10.
🔒 Nir Zuk Launches Cylake with $45M — Palo Alto Networks founder builds AI-native security for orgs that can’t touch public cloud.
🤖 Onyx Security Launches with $40M — Builds a secure control plane to govern autonomous AI agents across the enterprise.
🩹 Reclaim Security Raises $20M for Agentic Remediation — Hexadite founder’s new startup simulates business impact before deploying automated fixes.
🧪 Escape Raises $18M to Replace Manual Pentesting — Automates offensive security lifecycle with AI agents
🤖 OpenAI to Acquire Promptfoo — AI security testing startup ($23.6M raised) gets absorbed into OpenAI Frontier platform.
🔗 OX Security Launches Agentic Pentester — Continuous attack simulation that traces validated exploits back to the exact repo, file, and commit.
⚒️ Picks of the Week ⚒️
Stryker Hit by Devastating Iran-Linked Wiper Attack
Iran-linked hacktivist group Handala claims to have wiped over 200,000 servers, mobile devices, and systems and exfiltrated 50TB of data from medtech giant Stryker ($22.6B in 2024 sales, 56,000 employees), forcing offices across 79 countries to shut down 🤯. The group said the attack was retaliation for a U.S. missile strike on an Iranian school that killed more than 175 people, most of them children.
According to Krebs on Security, the attackers appear to have weaponized Microsoft Intune, Stryker’s own mobile device management platform, to issue mass remote wipe commands against enrolled devices. Employees in the U.S., Ireland, Australia, and India reported corporate laptops and personal phones wiped without warning, login pages defaced with Handala’s logo, and entire offices reverting to pen and paper. Staff with personal devices enrolled for work access lost personal data too.
Palo Alto Networks links Handala to Void Manticore, an actor affiliated with Iran’s Ministry of Intelligence and Security (MOIS). The group surfaced in late 2023 and has previously targeted Israeli civilian infrastructure and Gulf energy companies.
Stryker confirmed the attack in an SEC 8-K filing, acknowledging a global disruption to its Microsoft environment. The company says there is no indication of ransomware and believes the incident is contained, but has no timeline for full restoration.
This is a gut punch for healthcare. Stryker makes surgical equipment, joint replacements, defibrillators, and hospital beds used in operating rooms worldwide. When their systems go dark, hospitals are waiting for equipment and patients are waiting for care. I worked at Johnson&Johnson securing similar medical equipment. This is an absolute nightmare for everyone involved.
The Intune vector is particularly brutal: turning an orgs own management infrastructure into the weapon is the kind of move that should have every IT team auditing MDM admin access and conditional access policies this week.
Dig Deeper: Krebs on Security | Infosecurity Magazine | TechCrunch
Enforce Security Where Work Actually Happens
Keep Aware delivers Browser Detection and Response (BDR) to secure modern work where it actually happens—the browser. Monitor and govern GenAI usage, prevent sensitive data loss with browser-native DLP, and control extension risk before it becomes compromised. By analyzing real browser behavior, Keep Aware stops phishing, credential theft, and risky actions at the point of click, shifting security from reactive alerts to real-time prevention.
When the Code Generator Is Also the Code Auditor
Both Anthropic and OpenAI now ship SAST tooling: Claude Code Security scans for vulns using data flow context across files, while OpenAI’s Codex Security scanned 1.2M commits in its beta and flagged 792 critical and 10,561 high-severity findings across open-source projects including OpenSSH, GnuTLS, and Chromium. Mozilla is already using Claude to improve Firefox’s security posture.
The results are impressive, but there’s an uncomfortable question nobody is asking loudly enough: when the same model that generates your code is also the one reviewing it, who’s actually watching the henhouse?
Estimated cost sits around $15-25 per PR review, which i’d imagine matches up to what a SAST vendors charges when annualized. But consider the loop: an AI writes code, the same vendor’s AI reviews it, finds some issues, fixes them, and signs off.
I’m not saying they would intentionally do this, but a model is structurally unlikely to catch its own blind spots, and “we found and fixed the bugs our own tool introduced” is not the independent assurance most security programs are built on.
My friend James Wickett at DryRun Security actually just launched a report that derives real-world evidence on this exact topic. Worth checking out here.
$235M for the Founders Who Built Mandiant and Palo Alto
Two of the most consequential founders in security history officially came off the bench in the same week (although we covered Mandia’s moves nearly 2 months ago). Kevin Mandia (who sold Mandiant to Google for $5.4B) raised a cybersecurity-record $189.9M in combined seed and Series A for Armadin, an AI-driven attack simulation platform. Accel led, with GV, Kleiner Perkins, Menlo Ventures, In-Q-Tel, 8VC, and Ballistic Ventures participating. Armadin uses AI agents to model real adversary behavior across cloud, identity, and network infrastructure, producing validated attack paths instead of theoretical vuln scores.
Meanwhile, Nir Zuk (founder of Palo Alto Networks, CTO for 20+ years) launched Cylake with $45M in seed funding led by Greylock. Co-founded with Wilson Xu (former Palo Alto EVP of Engineering) and Udi Shamir (co-founder of SentinelOne), Cylake is building an AI-native security platform designed to run entirely on-prem or in private cloud for organizations that can’t touch the public cloud. Product availability is expected early 2027.
Combined, that’s $235M in seed/Series A capital behind two founders who already built category-defining companies. That’s a fair amount of funding to build great teams + product. As always, it comes down to execution and these two are masters at that.
Dig Deeper: Armadin Raises $189.9M | Cylake Launches with $45M | Greylock: Introducing Cylake
CISO Takes: What Separates Effective CISOs From the Rest
Two reads this week worth your time: Lenny Zeltser (former CISO at Axonius) distills six years of security leadership into a four-point framework, and SecurityWeek profiles Aimee Cardwell (former CISO at UnitedHealth Group, now CISO in Residence at Transcend) on the realities of running security at scale.
Attack surface reduction is the only way off the hamster wheel. Decommission unused SaaS, deactivate stale accounts, kill unnecessary systems. This lowers security costs and frees budget for strategic work.
Average CISO tenure is 3 years. Most leave before their foundational investments in identity architecture, attack surface reduction, and product security actually compound.
The defender’s advantage is terrain knowledge, not tools. Years in the role build understanding of which systems are truly critical, which vendors are real partners, and which risks the org has consciously accepted. No onboarding replicates that.
Burnout is a leadership problem, not a personal one. Cardwell gave her team “Flex Fridays” after major incidents. The result: measurable reduction in team burnout. People who feel seen stay longer and perform better.
Shadow AI is an attack surface problem disguised as a productivity problem. Cardwell’s approach: make the secure path the path of least resistance. If approved tools are harder to use than unapproved ones, you’ve already lost.
Dig Deeper: Zeltser: CISO Leadership Lessons | SecurityWeek: CISO Conversations with Aimee Cardwell
Scanner Raises $22M Series A Led by Sequoia Capital
Our friends and continuing sponsor of TCP have raised a $22M Series A led by Sequoia for reimagining how security teams search log data at scale. Scanner gives you blazing fast search across years of logs stored in object storage, without the SIEM-tier price tag. Their product is a game changer on many levels incl. DE, IR, hunting, and teams like Notion are building homegrown AI triage agents on top of it. Super cool.
This is one of my favorite products in SecOps right now, and the team behind it is just as sharp. Congrats to Cliff, Alex, and the Scanner crew. Well deserved.
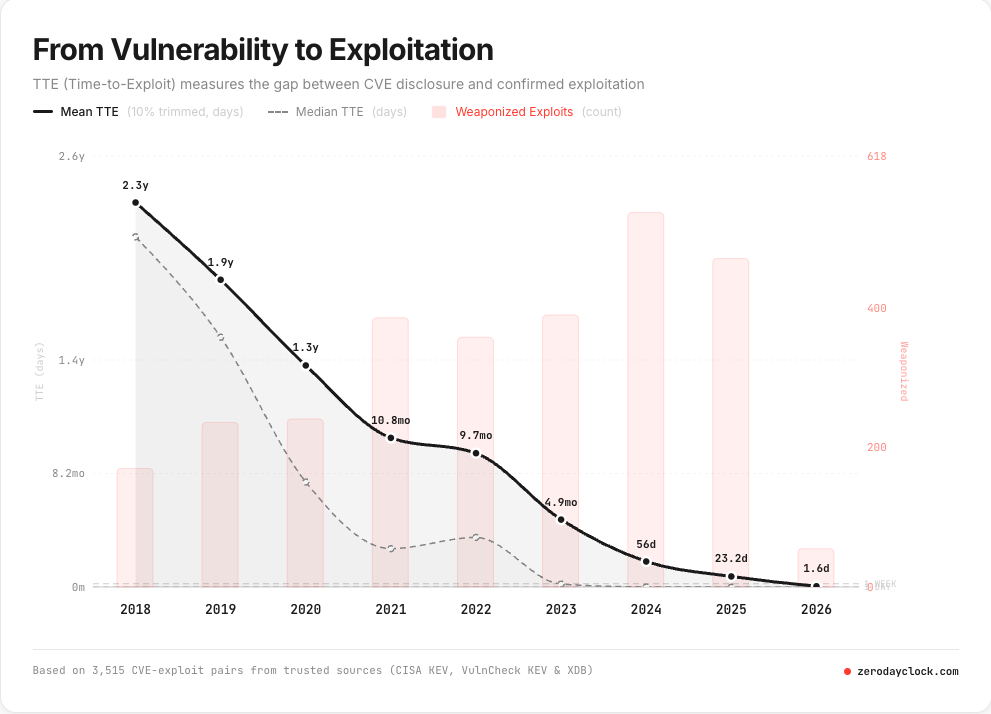
Zero Day Clock: The Exploitation Window is Collapsing to Zero
A new project called Zero Day Clock is tracking something every security team should internalize: the median time-to-exploit has collapsed from 771 days to just 6.36 days in five years, with nearly 40% of exploited flaws now weaponized before disclosure and over 44% exploited within 24 hours.
The site tracks TTE across 83,000+ CVEs from 10 sources including CISA KEV, ExploitDB, and Metasploit. The project maps milestones as TTE crosses thresholds: the 1-year mark was hit around 2021, 1 month around 2025, and 1 week in 2026, with 1-day and 1-hour marks projected for later this year and 1 minute by 2028.
When a vendor releases a patch, AI can now reverse-engineer it and generate a working exploit in minutes, but organizations still need an average of 20 days to test and deploy that same patch. Prioritization + attack surface reduction are the name of the game.
🎙️ [un]prompted Con Now Lives in NotebookLM
Every talk transcript and slide deck from the AI security conference has been loaded into Google’s NotebookLM, letting you chat with the full conference content, generate podcasts on any topic, or brief your team without rewatching hours of sessions. Brainchild of Rob T. Lee and one of the better examples of what an AI-native conference experience looks like after the event ends.
🔮 The Future of Security 🔮
AI Security
OpenAI to Acquire Promptfoo, to Bolster AI App Testing
OpenAI is acquiring Promptfoo, an open-source AI security evaluation platform that had raised $23.6M from Insight Partners and Andreessen Horowitz. Promptfoo’s tooling covers prompt injection, data leakage, jailbreak detection, and red-team simulations.
OpenAI buying its own testing layer signals that LLM security tooling is shifting from ecosystem play to platform feature.
More AI Security news ⬇️
AI Hands-On Lab for the Security Engineer #2: Governing MCP Servers with an AI Gateway in Azure
AI as Tradecraft: How Threat Actors Operationalize AI - Microsoft
Onyx Security launches operations with $40 million funding round
Browser Security
Push Security Adds Malicious Extension Detection, ClickFix Blocking
Push Security shipped malicious browser extension detection powered by its own threat research and public threat intel feeds, with options to auto-warn or block users and enforce extension allowlists/blocklists. Browser-native security keeps getting more relevant as identity and SaaS attacks shift into the browser.
Data Security
Jazz Exits Stealth with $61M for AI-Powered DLP
Jazz emerged from stealth with $61 million in combined seed and Series A led by Glilot Capital Partners and Team8. AI-native DLP.
More Data Security news ⬇️
Fraud Prevention
Darwinium Launches Agent Intent Intelligence
There’s an interesting shift taking place in agentic payments and commerce (think: sendmy agent to buy me the best fitness supps based on my Dr,’s recs). I hadn’t previously dug into this space before so it was certainly interesting to me.Security Operations
IoT/OT Security
Kai Emerges from Stealth with $125M
Kai launched with $125 million led by Evolution Equity Partners, building an agentic platform for IoT/OT. Co-founded by Claroty co-founder Galina Antova.
More IoT/OT Security news ⬇️
Offensive Security
OX Security Launches Agentic Pentester That Maps Exploits to Source Code
OX Security (founded by former Check Point execs) launched an agentic pentester that runs continuous attack simulations and traces each validated exploit back to the exact repo, file, and commit responsible. The pitch: other pentest tools stop at findings, OX maps the fix path to source code so AppSec and engineering aren’t just staring at another backlog.
More OffSec news ⬇️
Vulnerability Management
Reclaim Security Raises $20M to Close the Remediation Gap
Reclaim Security raised $20M in Series A led by Acrew Capital ($26M total) to build an autonomous remediation platform that simulates business impact before deploying fixes.
Interested in sponsoring TCP?
Sponsoring TCP not only helps me continue to bring you the latest in security innovation, but it also connects you to a dedicated audience of 20,000+ CISOs, practitioners, founders, and investors across 135+ countries 🌎
Bye for now 👋🏽
That’s all for this week… ¡Nos vemos la próxima semana!
Disclaimer
The insights, opinions, and analyses shared in The Cybersecurity Pulse are my own and do not represent the views or positions of my employer or any affiliated organizations. This newsletter is for informational purposes only and should not be construed as financial, legal, security, or investment advice.