The Biggest Supply Chain Attack of 2026 Was Unfolding While We Were at RSAC, the FBI Director's Gmail Got Popped, and a $10B AI Startup's Biometrics Hit the Auction Block
TeamPCP chained five ecosystems in eight days, Geordie AI won the Sandbox, $500M+ in funding dropped, and the biggest RSAC recap TCP has ever published
Welcome to The Cybersecurity Pulse (TCP)! I’m Darwin Salazar, Head of Growth at Monad and former detection engineer in big tech. Each week, I bring you the latest security innovation and industry news. Subscribe to receive weekly updates! 📧
A Practical Approach to Securing AI
If your organization is building or using AI, you understand how critical data exposure risk is becoming. Varonis Atlas was built to solve that - giving teams insight into all AI usage (including shadow AI), the ability to fix risky exposures, enforce runtime guardrails, and manage governance all in one platform.
Howdy 👋 - From RSAC to the TeamPCP software supply chain havoc, the past few weeks have been wild. I think this meme perfectly depicts what most of the industry is going through:
This post covers the biggest announcements and news from the past two weeks. But if you're looking for my unfiltered, practitioner-level takeaways from my time at RSAC this year, I dropped a deeper breakdown earlier this week:
TL;DR 🗞️
🔗 TeamPCP’s Cascading Supply Chain Attack — Trivy to LiteLLM to Axios to Mercor: one incomplete credential rotation turned into a 5-ecosystem, 8-day rampage
🤖 OpenAI Codex + GCP Vertex AI Vulns Disclosed — BeyondTrust and Unit 42 pop AI coding agents on basic AppSec failures while RSAC sells agent security
💰 XBOW Hits Unicorn at $120M Series C — GitHub Copilot creator’s autonomous pentesting platform reached #1 on HackerOne, first machine to outperform all human hackers
🆔 Oasis Security Raises $120M for Non-Human Identity — Craft Ventures led, Sequoia and Accel in; $195M total to build the access management layer for AI agents and machine identities
🛡️ Tenex Raises $250M Series B — One year old, agentic MDR that analyzes all telemetry within 60 seconds of ingestion
🏆 Geordie AI Wins RSAC Innovation Sandbox — Agent remediation via context engineering beats offensive security and code-level tooling for the crown
🇮🇷 FBI Confirms Hack of Director Patel’s Personal Email — Iranian-linked Handala group publishes ~300 emails from the FBI Director’s Gmail account
Plus: Delve’s fake compliance saga, a breathalyzer cyberattack stranding drivers, $160M+ in autonomous offensive security funding, 12 AI x Security product launches, and a whole lot more below 👇
Fair warning: this week’s issue is massive. Absurd amount of news across every domain, so I leaned on AI heavily to help me process, structure, and draft this one. Every take, every editorial call, and every fact-check is still me. But there’s no way I’m turning around a recap this comprehensive on my own, in a week, without it.
⚒️ Picks of the Week ⚒️
The Security Tool That Became the Weapon: Inside TeamPCP’s Supply Chain Campaign
The software supply chain didn’t just crack this month. It detonated.
TeamPCP executed a cascading campaign between March 19-27 that deliberately targeted the tools security teams trust most, chaining each compromise into the next across five ecosystems in eight days.
It started with Aqua Security’s Trivy, one of the most widely deployed open-source vulnerability scanners. TeamPCP used credentials retained from an incomplete February remediation to force-push malicious code to 75 of 76 trivy-action tags and publish poisoned binaries to GitHub Releases, Docker Hub, GHCR, and ECR. Tracked as CVE-2026-33634 (CVSS 9.4). It took five days to fully evict the attackers. Three days into remediation, they published additional malicious Docker images, proving access still hadn’t been severed.
From there, stolen credentials cascaded outward: a self-propagating npm worm (CanisterWorm) hit 64+ packages using blockchain-based C2 that can’t be taken down conventionally. Then Checkmarx KICS and AST GitHub Actions fell. Then LiteLLM, the open-source proxy routing API calls to 100+ LLM providers (95M monthly PyPI downloads). The poisoned versions used a .pth file that fires on Python interpreter startup without being imported or called. Three hours on PyPI at 3.4M daily downloads. Then Telnyx. Then the Axios npm package in a separate North Korean operation.
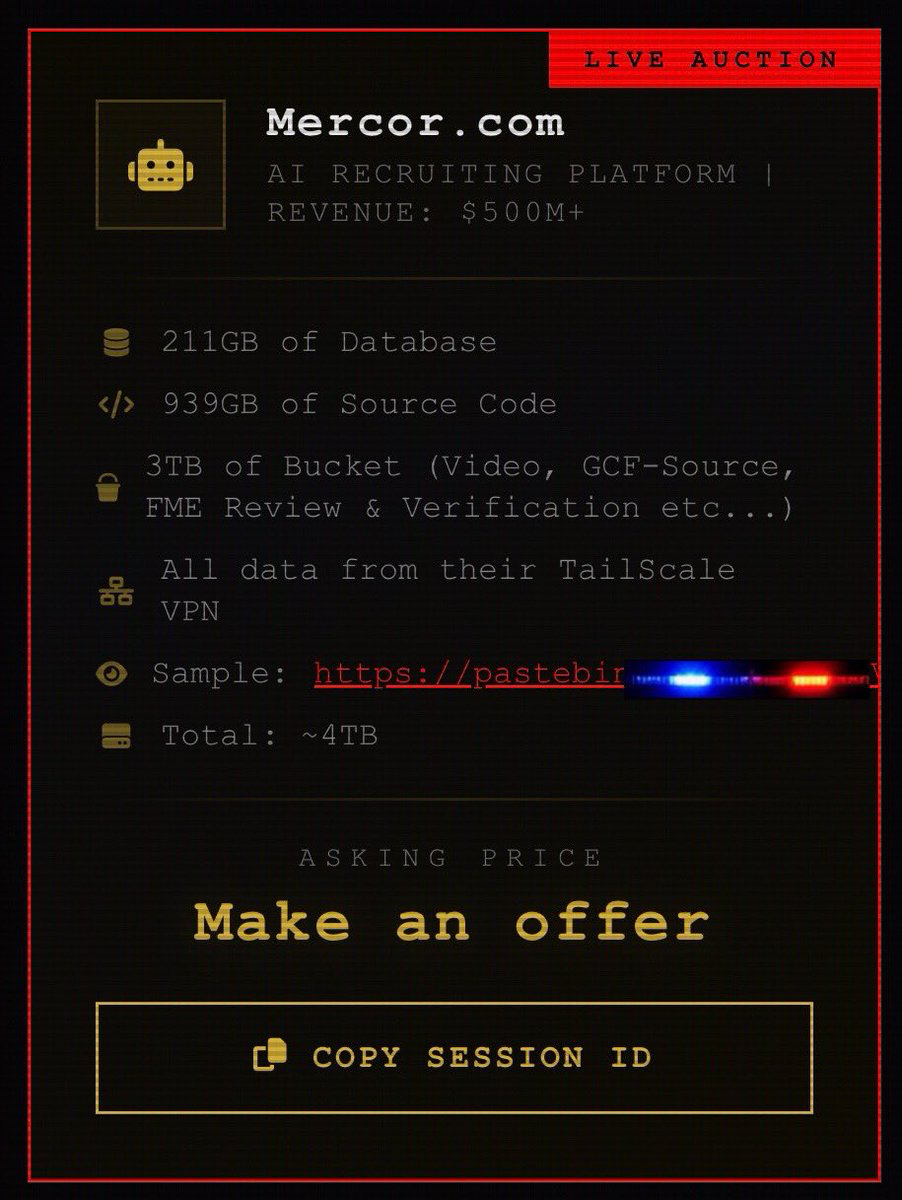
The downstream carnage hit Mercor, a $10 billion AI startup training models for OpenAI, Anthropic, and DeepMind. Reports indicate developers gave production credentials to an AI coding assistant running with unrestricted permissions. The compromised LiteLLM package came in through that pipeline. Lapsus is now auctioning 4TB: source code, database records, and 3TB of video interviews with face scans and KYC documents used for identity verification. Biometrics cannot be reset.
This is the story of the year. TeamPCP figured out that the open-source security tooling ecosystem is connected by credential chains, and if you pull on one thread, everything unravels. The most diligent organizations, the ones scanning every build, had the greatest exposure. The campaign started with a security scanner. Practical takeaways: pin to commit SHAs, not tags (71% of orgs still don’t, per Datadog). Treat every credential rotation as atomic or assume it’s incomplete. Audit your AI coding assistants’ permission scopes like you would a production service account. And know your transitive dependency tree, because the attackers already do.
Dig Deeper:Wiz | Datadog Security Labs | SANS | Endor Labs
Crush Insider Threats: Agent-to-Agent Security with Reco & Torq
Insider threats are evolving. Your defenses should too.
Agent sprawl, shadow AI, and disconnected tools leave your team chasing vague signals. Join Reco & Torq on April 15 to see how AI agents investigate insider threats in seconds, combining behavioral context with cross-stack signal orchestration to turn suspicious logins into confident verdicts automatically, with fewer false positives and faster MTTR.
AI Coding Agents Are Getting Popped on Fundamentals
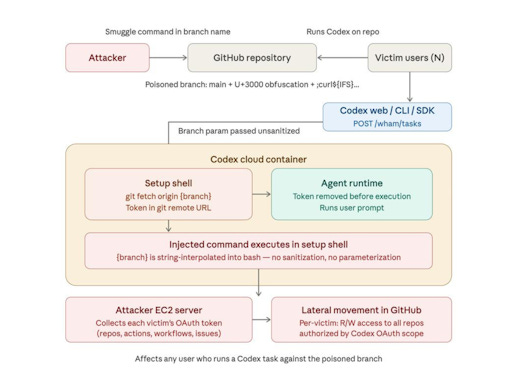
BeyondTrust Phantom Labs disclosed a critical command injection in OpenAI Codex that allowed theft of GitHub OAuth tokens via an unsanitized Git branch name. Codex passes branch names directly to the shell without validation. A malicious branch name (hidden behind 94 ideographic Unicode spaces and || true) could execute arbitrary commands inside the container, extracting the plaintext token that grants read/write access to the victim’s entire codebase. Set the poisoned branch as default, and every Codex user on that repo gets compromised. OpenAI classified it P1, patched February 5, 2026.
Separately, Palo Alto Networks Unit 42 showed how AI agents on Google Cloud’s Vertex AI could be weaponized into “double agents” by exploiting overly broad default service agent permissions (P4SA). Researchers extracted credentials from a deployed agent and pivoted to unrestricted read access across Cloud Storage buckets, restricted Google-owned Artifact Registry repos, and internal Dockerfiles. Google updated its docs and now recommends Bring Your Own Service Account (BYOSA).
Branch name injection. Default OAuth scopes covering Google Workspace. Basic AppSec hygiene failures in a new context, while RSAC was wall-to-wall “agent security” product launches.
Dig Deeper: BeyondTrust Phantom Labs writeup | Unit 42 Double Agents research | SecurityWeek coverage
Geordie AI Wins RSAC Innovation Sandbox
Geordie AI took home the Innovation Sandbox title at RSAC 2026, beating out nine other finalists (each received $5M in investment). The company launched Beam, an AI agent remediation suite built on context engineering that continuously assesses risk and feeds mitigation back to agents in real time. Think guardrails that adapt to what the agent is actually doing rather than what you hoped it would do. Founded by Henry Comfort (ex-Darktrace COO Americas) and Benji Weber (ex-Snyk), the team went from buying laptops a year ago to winning the industry’s most prestigious startup competition.
Innovation Sandbox winners always signal where the industry’s head is at. Agent remediation winning over offensive security and code-level tooling tells you where buyer anxiety is right now. “Context engineering” is a term we’ll be hearing a lot more of. Whether Geordie can scale beyond the hype is the question, but the thesis is solid.
Cyberattack on Breathalyzer Company Leaves Drivers Stranded Across the US
Intoxalock, a company that makes court-mandated vehicle breathalyzer ignition interlock devices, confirmed a cyberattack on March 14 that knocked its systems offline and left drivers across the country unable to start their cars. The devices require periodic calibration, and the outage prevented calibration resets, effectively bricking vehicles for users who are legally required to have the devices installed.
Cyber-physical impact on vulnerable populations. People under court order who literally cannot drive to work, medical appointments, or childcare because a vendor got popped. If your device can be remotely bricked by a backend outage, your architecture is a liability.
Delve Whistleblower Doubles Down With Alleged Receipts on ‘Fake Compliance’
The Delve saga escalated again. Hours after CEO Karun Kaushik published a lengthy denial on X, anonymous whistleblower “DeepDelver” fired back with what they claim is video evidence and Slack messages backing up allegations that the Y Combinator-backed compliance automation startup ($32M Series A, valued at ~$300M) fabricated compliance data for customers. The original leak reportedly included 493 draft audit reports with 99.8% identical boilerplate text.
If even a fraction of these allegations hold up, this is a body blow to the automated compliance space. If a well-funded, YC-backed player was allegedly generating rubber-stamp audits, every CISO relying on automated compliance platforms is going to start asking harder questions about what’s actually behind the curtain.
FBI Confirms Hack of Director Patel’s Personal Email
Iranian-linked hacking group Handala claimed responsibility for breaching FBI Director Kash Patel’s personal Gmail account, publishing roughly 300 older emails along with photos and documents. The FBI confirmed the breach but stated the materials were “historical in nature” and contained no government information. The hack came shortly after the FBI seized Handala’s domains and announced a $10M reward for information on the group’s members, following their claimed attack on medical tech company Stryker.
“No government information” is doing a lot of heavy lifting in that statement. Personal email of the FBI Director is still useful for social engineering, relationship mapping, and reputational targeting. Another data point in the escalating US-Iran cyber conflict. If the FBI Director’s Gmail gets popped, your executives’ personal accounts are absolutely in scope for your threat model.
🔮 The Future of Security 🔮
AI x Security
RSAC 2026 had one message: agentic AI is in production and everyone wants to sell you the guardrails. The conference floor was wall-to-wall “agent security” launches. At least a dozen vendors shipped products targeting the same core problem: autonomous agents now have access to credentials, source code, production infrastructure, and elevated permissions, and nobody has a consistent way to discover what’s running, govern what it’s allowed to do, or enforce policy at runtime.
The market has split into three lanes: discovery (find your shadow agents), governance (write and enforce policy), and runtime enforcement (stop bad behavior in real time). MCP server security emerged as the new checkbox everyone is racing to claim.
The Big Announcements:
NVIDIA launched OpenShell and NemoClaw, an open-source runtime that puts out-of-process policy enforcement between autonomous agents (“claws”) and your infrastructure: sandboxing, permission verification, and a privacy router that keeps sensitive context on local models
CrowdStrike unveiled Charlotte AI AgentWorks, a no-code agent development platform with launch partners including Anthropic, OpenAI, NVIDIA, AWS, Salesforce, and Accenture
Palo Alto Networks shipped Prisma AIRS 3.0, covering the full agentic lifecycle from discovery to runtime with an AI Agent Gateway and agentic endpoint security (via the pending Koi acquisition)
Wiz (now Google Cloud) introduced AI-APP, an AI Application Protection Platform treating AI as an interconnected system across models, agents, and data, plus a Red Agent for AI-powered offensive testing
Snyk launched Agent Security and brought Evo AI-SPM to GA, using automated agents to build a live AI Bill of Materials and enforce governance across the coding agent lifecycle
Sysdig released runtime security for AI coding agents, detecting credential exposure, reverse shells, binary tampering, and unauthorized file access across tools like Claude Code, Codex, and Gemini
Rubrik unveiled SAGE (Semantic AI Governance Engine), using a custom SLM to interpret natural-language policies and enforce them in real time
Astrix expanded into full AI agent discovery and enforcement via its Agent Control Plane
Nudge Security extended its platform to AI agent discovery alongside its existing SaaS security
Apiiro launched AI Threat Modeling within Guardian Agent, generating architecture-aware threat models from tickets and design specs before code exists
Straiker launched Discover AI and expanded Defend AI, with 12,000+ MCP vulnerability databases and runtime tracing across coding agents, productivity tools, and custom agent platforms
F5 and Forcepoint partnered to secure enterprise AI data from creation through runtime operations
Application Security
AI is writing code faster than humans can review it. The industry is splitting into two camps. One is better detection: combining AI reasoning with deterministic analysis to catch logic flaws that traditional SAST misses entirely. The other is runtime protection: watching what code actually does in production, because signatures can’t keep up when time-to-exploit approaches zero.
Semgrep launched Multimodal, pairing its rule-based engine with LLM reasoning to catch business logic flaws like IDORs and auth bypasses. Already finding zero-days at customer deployments. Custom Workflows (Python-based automated pipelines for detection, triage, and remediation) are in private beta.
Raven raised $20M (Norwest led, with SentinelOne participating) for CVE-less runtime behavioral security. The platform maps execution chains inside running applications and generates behavioral fingerprints to detect malicious deviations in real time, even without known vulns. Three U.S. patents filed.
Qodo raised $70M Series B (Qumra Capital led, $120M total) for AI-powered code verification. The bet: as tools like OpenClaw and Claude Code generate billions of lines of code monthly, verifying that software works as intended is the bottleneck.
Cloud Security
One announcement worth calling out: CrowdStrike shipped adversary-informed cloud risk prioritization in Falcon Cloud Security. CrowdStrike’s answer connects live application behavior to active adversary tradecraft in a single model. Three new capabilities: Application Explorer (runtime view of how app behavior shapes cloud risk), Timeline Explorer (chronological root-cause analysis of config and app changes), and a Cloud Risk Engine that maps exposures to real adversary TTPs.
Email Security
Sublime Security shipped ADÉ (Autonomous Detection Engineer) to GA. ADÉ is an AI agent that turns novel email attacks into new detections autonomously, going from reported threat to accepted detection in hours instead of weeks. The agent can run end-to-end without analyst intervention: picking up a newly reported threat, generating detection logic, and accepting high-confidence coverage. For teams drowning in phishing variants, this is detection engineering on autopilot.
Exposure Management
Censys raised $70M ($40M Series D from Morgan Stanley Expansion Capital + $30M debt; $149M total). Building AI-driven solutions on top of its continuously updated global map of internet infrastructure.
Onit Security emerged from stealth with $11M seed (Hetz Ventures and Brightmind Partners led). Founded after an Iranian state-sponsored attack exploited a known vuln buried in co-founder Ofer Amitai’s previous company’s backlog. Onit’s agentic platform automates the full exposure lifecycle: AI agents prioritize by business context rather than CVSS, auto-identify asset ownership, and execute fixes. Founding team has three prior acquisitions: SCADAfence (Honeywell), Portnox, and For-Each (Autodesk).
Identity and Access Management
Identity was RSAC’s quiet blockbuster. BeyondTrust data showed a 466.7% increase in enterprise AI agents over the past year, most deployed through low-code platforms with privileges that rival human admins. Non-human identity management and agentic access governance emerged as the hottest sub-categories, with massive funding and product launches all converging on the same problem.
Oasis Security raised $120M Series B (Craft Ventures led; Sequoia, Accel, Cyberstarts participated; $195M total). Shipped Agentic Access Management (AAM): intent-based, just-in-time access for AI agents and machines that evaluates what a system is trying to do before granting permissions.
ConductorOne launched AI Access Management, a unified control plane for governing AI tools, agents, and MCP connections. 3,000+ hosted MCP servers let any API-connected app be governed out of the box, with fine-grained tool call authorization and credential vaulting. AI agents are treated as first-class identities.
BeyondTrust expanded its Pathfinder Platform to secure AI agent “coworkers” alongside human and machine identities under a single privilege model. Phantom Labs research found most enterprises run shadow AI agents with privileged access that security can’t see. Endpoint Privilege Management now enforces least privilege for AI clients (Claude, ChatGPT) on endpoints.
IoT/OT Security
Eclypsium raised $25M in strategic funding (PEAK6 Strategic Capital led, $110M total). Secures firmware, software, and hardware across enterprise device fleets. The new capital is earmarked for expanding into AI infrastructure: NVIDIA GPU servers in AI datacenters, Bluefield DPU-based appliances, CCTV cameras, 5G networking gear, and SASE/SD-WAN edge appliances.
Offensive Security
Autonomous offensive security had the biggest funding week of any sub-category at RSAC. $160M+ hit this space, and AWS made it a first-party service.
XBOW raised $120M Series C (DFJ Growth and Northzone led, $237M total, valuation $1B+). Founded by GitHub Copilot creator Oege de Moor, XBOW’s autonomous platform reached #1 on the HackerOne leaderboard, the first time a machine outperformed all human hackers on the platform. Sequoia, Altimeter, and Alkeon also in the cap table.
RunSybil raised $40M (Khosla Ventures led, with Anthropic’s Anthology Fund participating). Co-founded by OpenAI’s first security researcher and Meta’s former offensive security red team lead. Black-box AI agents conduct continuous pentesting without source code access, chaining vulns like human attackers. Customers include Cursor and Notion.
AWS Security Agent hit GA for on-demand penetration testing across six regions. Autonomous pentesting at $50/task-hour (avg. test ~$1,200), supporting multicloud (AWS, Azure, GCP, on-prem).
Security Operations
Last year’s RSAC was “we’re building an agentic SOC.” This year’s was “here’s the receipt.” The difference is that vendors are now shipping GA products, acquiring purpose-built startups, and embedding multi-agent architectures into existing platforms. Whether any of it actually works at scale in production is still TBD, and Gartner publishing an evaluation framework for AI SOC agents suggests the analyst community shares that skepticism. But the investment thesis is clear: SOC teams can’t hire their way out of alert volume, and AI agents are the bet.
The Big Announcements:
Tenex raised $250M Series B (Crosspoint Capital led) just a year after launch. Agentic MDR that ingests and analyzes all available telemetry within a minute. AI triages, investigates, and documents; humans make final calls.
Rapid7 acquired Kenzo Security to bring multi-agent AI into its Command Platform. Kenzo’s entity-centric data mesh unifies endpoint, identity, cloud, and SaaS data to power autonomous alert investigations. The play: move Rapid7’s MDR from AI-assisted to AI-driven.
Databricks entered the security market with Lakewatch, an open agentic SIEM built on its lakehouse architecture. The pitch: decouple compute from storage, retain all your telemetry in open formats, and deploy AI agents for detection and triage where the data already lives. Acquired SiftD.ai (founded by the creator of Splunk’s SPL) and Antimatter to bolster the stack. Anthropic’s Claude models power parts of the platform, and Anthropic itself uses Databricks for its own security lakehouse. Adobe and Dropbox are early customers. In private preview.
Accenture and Anthropic partnered to scale AI-driven cybersecurity operations, combining Accenture’s managed security services with Anthropic’s Claude models.
Wiz shipped the Blue Agent to GA, joining its Red and Green Agents to power agentic workflows across AI environments.
Datadog launched Bits AI Security Analyst for Cloud SIEM (GA globally). Autonomously investigates alerts using unified security and observability data.
Torq released Agentic Builder, turning natural language descriptions of security goals into production-grade AI agents and workflows.
Dropzone AI launched AI Threat Hunter, an autonomous agent for continuous proactive threat hunting.
Geordie AI introduced Beam, the first AI agent remediation suite using context engineering. Geordie also won the RSAC Innovation Sandbox (each finalist received $5M).
Manifold raised $8M seed (Costanoa Ventures led) for its AI Detection and Response (AIDR) platform. Built by the creators of LLM Guard, Manifold monitors agent behavior at runtime on endpoints, mapping connections to MCP servers and external systems. Agentless, deploys in days.
Interested in sponsoring TCP?
Sponsoring TCP not only helps me continue to bring you the latest in security innovation, but it also connects you to a dedicated audience of 20,000+ CISOs, practitioners, founders, and investors across 135+ countries 🌎
Bye for now 👋🏽
That’s all for this week… ¡Nos vemos la próxima semana!
Disclaimer
The insights, opinions, and analyses shared in The Cybersecurity Pulse are my own and do not represent the views or positions of my employer or any affiliated organizations. This newsletter is for informational purposes only and should not be construed as financial, legal, security, or investment advice.









RSA week is always a crazy hectic time in cyber! Great recap.